
Welcome to the Experian Thought Leadership Hub
Gain insights into the fast-changing world of consumer and business data through our extensive library of resources.
387 resultsPage 1
 Webinar
Webinar
Experian experts discuss how companies are integrating credit education, identity protection, and financial wellness into their employee benefits offerings.
Watch our on-demand webinar to discover:
 Tip Sheet
Tip Sheet
Insights from Experian’s 2026 Mortgage Lender Playbook to help lenders drive growth and resilience:
 Infographic
Infographic
Recoveries hinge on knowing who can pay, not just who owes. This infographic explores how debt buyers and collections agencies can better identify signals of true payment capacity.
Did you know?
Read the infographic for more insights and strategies to drive smarter recoveries.
1Household Debt and Credit report, Q3 2025, Federal Reserve Bank of New York.
2Debt Collection Industry Statistics, zipdo.
3Collections Industry Statistics, Gitnux.
 Report
Report
Learn how you can move beyond single-point employee benefit solutions and embrace a more holistic approach that combines:
 Webinar
Webinar
The credit marketing landscape is evolving. As competition intensifies and consumer expectations rise, financial institutions that can predict, personalize and perform at scale will define the next generation of success.
In this webinar, our experts explore how financial institutions can use connected intelligence to find, know and grow the right customers, leading to:
 Report
Report
As the credit card landscape evolves, understanding how consumers and businesses are adapting has never been more important.
Our second annual State of Credit Cards Report provides a timely update on key market dynamics and dives into an often-overlooked segment within credit card portfolios: business accounts.
Key takeaways:
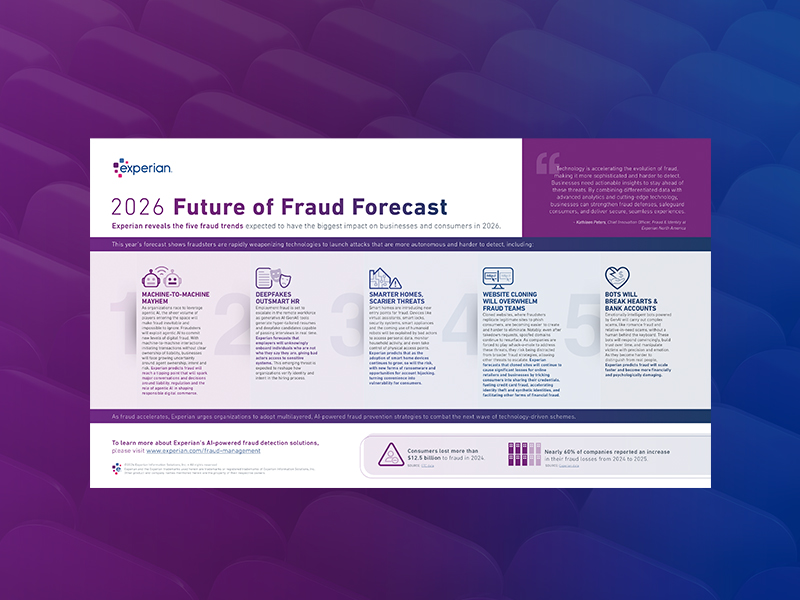 Infographic
Infographic
Download Experian’s 2026 Future of Fraud Forecast to explore five fraud trends expected to have the biggest impact on businesses and consumers in the coming year, including:
The Regional Economic Health Tracker examines consumer health across the four U.S. census regions. It highlights how regional dynamics, from data center growth to housing costs and credit conditions, are shaping household finances today.
 Infographic
Infographic
As market conditions shift, collections success depends on continuous, high-quality consumer data. This checklist highlights how always-on collections intelligence can help debt buyers and agencies: