
Welcome to the Experian Thought Leadership Hub
Gain insights into the fast-changing world of consumer and business data through our extensive library of resources.
418 resultsPage 1
 Report
Report
See how a single attacker leveraged fraud ring tactics to compromise over 50 accounts in under 30 days—and how to detect and stop solo account takeover attacks at scale.
Key insights:
 Report
Report
Consumers have powered the U.S. economy through repeated shocks, but new pressures are testing their resilience. As energy prices rise and economic conditions shift, the outlook is becoming more uncertain.
 Report
Report
Explore how modern fraudsters use coordinated, strategic attack methods—and learn how to detect, disrupt and prevent them using behavioral intelligence and real-time insights.
Key insights:
 Report
Report
Uncover a coordinated account takeover fraud ring in action and learn how it was stopped using behavioral, device and network intelligence.
Key insights:
 Infographic
Infographic
Download the latest Alternative Financial Services Trend Report to reveal new insights on growth and risk, including:
 Webinar
Webinar
In this webinar, Experian experts explore how organizations can apply proven consumer fraud prevention tactics to strengthen commercial lending defenses.
What you'll learn:
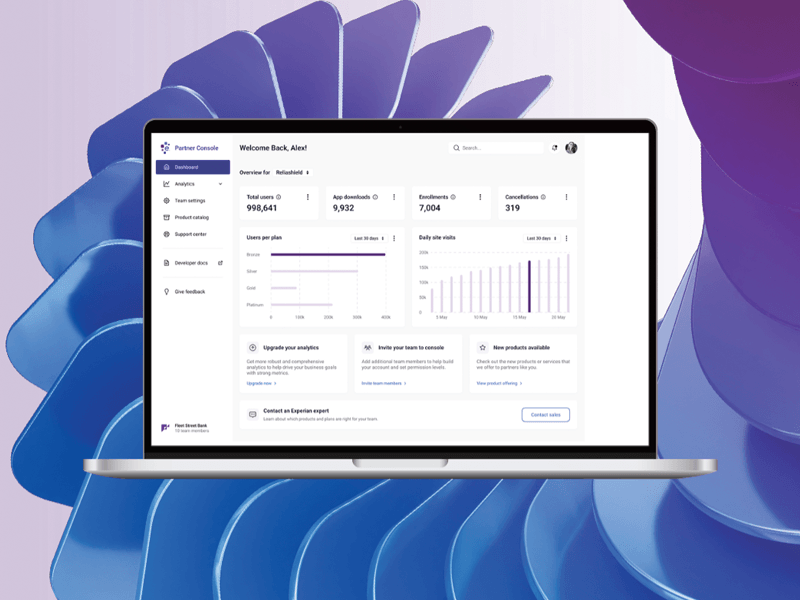 Infographic
Infographic
Discover a faster, more efficient way to bring financial wellness and privacy solutions to market. Learn how to:
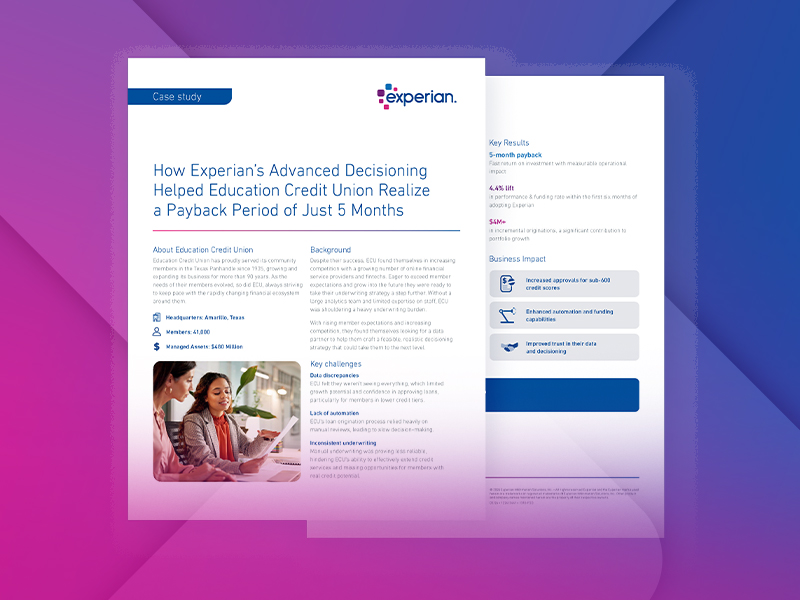 Case Study
Case Study
Education Credit Union modernized underwriting with Experian’s Advanced Decisioning—driving faster decisions, stronger approvals, and rapid ROI in a competitive market.
 Webinar
Webinar
Gain a clearer view of how consumers earn, spend, and manage their money in today’s evolving economic landscape. In this webinar, Experian experts break down the financial behaviors shaping demand, risk, and growth—using macroeconomic trends, credit data, and transaction-level cash flow insights.