Telecommunications, Cable & Utilities
Telecommunications, Cable & Utilities

The financial services industry continues to face mounting pressures to meet the highest standards of data reporting and accuracy. New regulations and mandates are introduced regularly, impacting the way companies do business. And a more credit-educated consumer base is seeking insights into their own credit data, providing a separate second of eyes that demand accuracy. Not only has the Fair Credit Reporting Act (FCRA) set requirements on dispute investigation and response, but the Consumer Financial Protection Bureau (CFPB) is also paying close attention. Recent announcements indicate the CFPB wants more information about the credit eco-system to gain more data about consumer disputes. According to the CFPB, it’s a joint problem – “the NCRAA’s, data furnishers, public record providers, and consumers all play roles which affect the accuracy of the information with credit reports.” And it’s not just the big banks that are being targeted with fines. The CFPB has made it clear it will also direct attention to certain nonbanks and financial products. In today’s data-driven environment, there are roughly 12,000-plus data furnishers, resulting in more than one billion pieces of information being updated on a monthly basis. Over 220 million consumers have some form of credit information attached to them, and transactional data is flowing all the time. Fail to update and a furnisher will quickly see flaws in their reporting. In fact, a recent study revealed an estimated 2.1% of contact info goes bad if unattended for more than one month. Clearly, achieving data quality is an ongoing investment for any organization, but companies often lack a clean plan. Some data furnishers fail to report, or elect to report to just one bureau, even though providing better data will result in a more complete and accurate credit profile. So how do you tackle the challenge of data quality? Organizations should consider implementing these six steps: Review data governance. Correct errors in data submissions. Complete an audit of data submissions. Evaluate disputes and resolutions. Compare data to peers and the industry. Review existing policies and processes. Follow these steps and your organization will earn a reputation among both regulators and consumers for clean, credible data. Plus, the investment in better data will reduce the need to resolve future disputes and fines. To learn more about meeting your FCRA responsibilities and best practices around data quality, check out our on-demand webinar or data integrity services site.

It’s official. Millennials have surpassed Baby Boomers in population size, according to the US Census. And while they are quick to adopt the “selfie” and all things social, they have been slow to embrace the world of credit. Sure, there’s been increased regulation over the past decade, and coming into adulthood in the midst of the Great Recession hasn’t helped. But don’t count Millennials out of the credit game just yet. A deeper, more segmented view of this digital-dependent generation shows a very diverse population with plenty of opportunity for lenders. Plus, their sheer size in numbers and $200 billion in annual buying power demand financial institutions evolve to accommodate this massive market. As Gen Y comes of age, there is growing evidence they are open to building and growing their personal credit history. But if financial institutions wish to capture the attention and business of this demographic, they must adapt, leveraging deeper segmentation insights with more effective prospecting strategies to reach them. Experian's data reveals key trends in terms of how this generation is utilizing credit, tips and tools to find the most credit-ready individuals, and strategies to grow the thin-file Millennials as they come of age. “Given the significance millennials play in financial services and the credit marketplace, it is crucial to understand this influential consumer segment and how they use credit as a tool,” said Michele Raneri, vice president of analytics and business development. “While this generation may not look like they are on the right track financially, it’s important to keep in mind that credit scores are built on credit experiences, and while this generation has been slower to use credit, they have plenty of opportunities to build a positive credit history.” To learn more about Millennials and credit, visit Experian.com/millennials.

Electronic signatures and their emerging presence in our Internet-connected world I had the opportunity to represent Experian at the eSignRecords 2015 conference in New York City last week. The concept of electronic signature, while not new, certainly has an emerging presence in the Internet-connected world — as evidenced by the various attendee companies that were represented, everything from home mortgages to automobiles. Much of the discussion focused on the legal aspects of accepting an electronic signature in lieu of an in-person physical signature. The implications of accepting this virtual stamp of approval were discussed, as well as the various cases that already have been tried in court. Of course, the outcome of those cases shapes the future of how to properly integrate this new form of authorization into existing business processes. Attendees discussed the basic concept of simply accepting a signature on an electronic pad as opposed to one written on a piece of paper. That act alone has many legal challenges even though it provides the luxury of in-person authentication through a face-to-face meeting. The complexities and risk increase exponentially when these services are extended over the Internet. The ability to sign documents virtually opens up a whole new world of business opportunities, and the concept certainly caters to the consumer’s need for convenience. However, the anonymity of the Internet presents the everyday challenge of balancing consumer expectations of greater ease of use with necessary fraud prevention measures. Ultimately, it always comes back to understanding who is actually signing that document. All of this highlights the need for robust authentication and security measures. As more and more legal documents and contracts are passed around virtually, the opportunity to properly screen and verify who has access to the documents gets more critical. Many organizations still rely on the tried-and-true method of knowledge-based authentication (KBA), while many others have called for its end. KBA continues to soldier on as an effective way to ensure that people on the other end of the wire are who they say they are by asking questions that — presumably — only they know the answers to. In most cases, KBA is viewed as a “check the box” step in the process to satisfy the lawyers. In certain cases, that’s all you need to do to ensure compliance with legal policy or regulatory requirements. It starts to get tricky is when there’s more on the line than just “check the box” actions. When the liability of first- or third-party fraud, becomes greater than simple compliance, it’s time to implement tighter security, while at the same time limiting the amount of friction caused by the process. Many in attendance discussed the need for layers of authentication based on the type of documents that are being processed and handled. This speaks directly to the point that one size does not fit all. As the industry matures and acceptance of e-signatures increases, so too does the need for more robust, flexible options in authentication. Another topic — that was quite frankly foreign to everyone we talked to — was the need for security around the concept of account takeover. When discussing this type of fraud, most attendees did not even consider this to be a hole in their strategy. Consider this fictional scenario. I’m responsible for mergers and acquisitions for my publicly traded company. I often share confidential information via electronic means, leveraging one of the many electronic signature solutions on the market. I become a victim of a phishing attack and unknowingly provide my login credentials to the fraudster. The fraudster now has access to every electronic document that I have shared with various organizations — most of which have been targets for mergers and acquisitions. Fraudsters are creative. They exploit new technologies — not because they’re trendsetters, but because oftentimes these new technologies fail to consider how fraudsters can benefit from the system. If you are considering adopting e-signature as a formal process, please consider implementing: Flexible levels of authentication based on the risk and liability of the documents that are being presented and what they are protecting FraudNet for Account Takeover, which enhances security around access to these critical documents to protect against data breaches Not only the needs and experiences of your own business, but customer needs as well to enable to the best possible customer interactions If you haven’t considered implementing e-signature technology into your business process, you should — but be sure to have your fraud team present when considering the implementation.

Imagine the following scenario: an attacker acquires consumers’ login credentials through a data breach. They use these credentials to test account access and observe account activity to understand the ebbs and flows of normal cash movement – peering into private financial records – verifying the optimal time to strike for the most financial gain. Surveillance and fraud staging are the seemingly benign and often-transparent account activities that fraudsters undertake after an account has been compromised but before that compromise has been detected or money is moved. Activities include viewing balances, changing settings to more effectively cover tracks, and setting up account linkages to stage eventual fraudulent transfers. The unfortunate thing is that the actual theft is often the final event in a series of several fraudulent surveillance and staging activities that were not detected in time. It is the activity that occurs before theft that can severely undermine consumer trust and can devastate a brand’s reputation. Read more about surveillance, staging and the fraud lifecycle in this complimentary whitepaper.

Soaring in the solar energy utility market By: Mike Horrocks and Rod Everson The summer is a great time of the year - it kicks off summer and the time to enjoy the sunshine and explore! It is also for me the recognition that days now are only getting shorter and makes me think about my year goals and am I going to hit them. In this spirit of kicking off summer, I thought I would talk about three opportunities that the utility vertical could and should take advantage of. 1. The future of Solar Photovoltaics (PV) is just getting brighter A recent study called out an expected 25 percent jump in Solar PV installs over the previous year. This is jump is just another in a long line of solar install records. While the overall cost of these installs has dropped, one must ask whether the accessibility is there for everyone. The answer is not yet. A potential opportunity may come in the form of community solar as an advantage over rooftop solar. This scenario involves a utility installing an array of PV cells and then carving out a specific cell for an individual residential customer for lease, crediting his or her bill at a percentage of the cost. 2. Generations are bringing change Just as spring gives way to summer, summer will give way to fall. The same is true in the utility markets on many fronts. At a larger infrastructure scale, utilities have to think about the kind of plants and capital investments they want to make. Another report indicated that 60,000 megawatts of coal energy is going to be retired over the next four years. This obviously will change the capital decision making functions in the industry. At a more personal level, however, there are changes in the consumers and their behaviors as well. Are those changes being accounted for in your organization? Is the next generation of consumers and the products and services it will demand being formulated in your strategy? How will you identify those consumers and secure them as customers? For example, while electrical energy consumption has been decreasing, what would be the impact if there was a revolution in battery technology? What if charging an electric automobile battery became as fast as filling a tank of gas? What if the battery gave you the same mileage range as a tank of gas and did it at a lower cost per mile? Would electric usage spike? 3. Blackouts happen; be prepared The best-laid plans sometimes still cannot account for those acts of God that cause disruptions to the grid. Blackouts happen, and if you don’t have flashlights with new batteries, you will be left in the dark. The same uncertainty is inevitable in the utility vertical. In the 2015 PwC Power and Utility Survey, 3 percent of the respondents said that there would be minor disruptions in business models, with the rest saying the disruptions would range from moderate to very disruptive. In fact, more than 47 percent of respondents said the changes would be very disruptive. What kind of flashlight-and-fresh-batteries strategy will you employ when the lights go out? Are your decision strategies and risk-management practices based on outdated solutions or approaches? Consider whether your business can take advantage of these situations. If you’re not sure, let’s set aside some time to discuss it, and I can share with you how Experian has helped others. There are still many sunny days ahead, but act now before the seasons change and you and your strategies are left out in the cold.

Customer experience strategies for success Sometimes it’s easier to describe something as the opposite of something else. Being “anti-” something can communicate something meaningful. Cultural movements in the past have taken on these monikers: consider the “anti-establishment” or “anti-war” movements. We all need effective anti-virus protection. And there are loads of skin products marketed as “anti-aging”, “anti-wrinkle”, or “anti-blemish.” But when you think about a vision for the customer experience that your company aspires to deliver, this approach of the “anti-X” falls flat. Would you want to aspire to basically “not stink?” Would that inspire you and your team to run through walls to deliver on that grand aspiration? Would it motivate customers to stick with you, buy more of what you sell, and tell others about you? I think not…But it sure seems like many out there indeed do aspire to “not stink.” Sure, there are great companies out there who have a set a high standard for customer experience, placing it at the center of their strategies and their success. Some, like Zappos, started that way from the beginning. Others, like The Ritz-Carlton, realized that they had lost their way and made the commitment to do the hard work of reaching and sustaining excellence. On the other hand, there are hundreds of firms who have a weak commitment to or even understanding of the importance of customer experience to their strategy and performance. Their leaders may give lip service or just pay attention for a few days or hours following the release of reports from leading analysts and firms. They may have posters and slogans that talk about putting the customer first or similar platitudes. These companies probably even have talented and passionate professionals working tirelessly to improve the customer experience in spite of the fact that nobody seems to care much. What these firms lack is a clear customer experience strategy. As nature abhors a vacuum, customers and employees are free to infer or just guess at it. Focusing on customer experience only when a report comes out – and paying special attention only when weak results put the firm near the bottom of the ranking leads people to conclude that all that really matters is to “not stink.” In other words, don’t stand out for being bad…but don’t worry much about being good as it is not important to the company’s strategy or results. I think that this “don’t stink” implicit strategy helps explain a fascinating insight from a Forrester survey in 2013: “80% of executives believe their company is delivering a superior customer experience, yet in 2013 only 8% of companies surveyed received a top grade from their customers.” Many leaders simply have not invested the energy and commitment necessary to define a real customer experience vision that reflects a deep understanding of the role that it plays in the company’s strategy. Beyond setting that vision, there is a big and sustained commitment required to deliver on the vision, measure results, and continuously adjust as customer needs evolve. Like all journeys, a great customer experience starts with one step. Establishing a customer experience strategy is the first one – and “don’t stink” simply stinks as a strategy. Download our recent perspective paper to learn how exceptional customer experience can give companies the competitive edge they need in a market where price, products and services can no longer be a differentiator.

If rumors hold true, Apple Pay will launch in a week. Five of my last six posts had covered Apple’s likely and actual strategy in payments & commerce, and the rich tapestry of control, convenience, user experience, security and applied cryptography that constitutes as the backdrop. What follows is a summation of my views – with a couple of observations from having seen the Apple Pay payment experience up close. About three years ago – I published a similar commentary on Google Wallet that for kicks, you can find here. I hope what follows is a balanced perspective, as I try to cut through some FUD, provide some commentary on the payment experience, and offer up some predictions that are worth the price you pay to read my blog. Source: Bloomua / Shutterstock.com First the criticism. Apple Pay doesn’t go far enough: Fair. But you seem to misunderstand Apple’s intentions here. Apple did not set out to make a mobile wallet. Apple Pay sits within Passbook – which in itself is a wrapper of rewards and loyalty cards issued by third parties. Similarly – Apple Pay is a wrapper of payments cards issued by third parties. Even the branding disappears once you provision your cards – when you are at the point-of-sale and your iPhone6 is in proximity to the reader (or enters the magnetic field created by the reader) – the screen turns on and your default payment card is displayed. One does not need to launch an app or fiddle around with Apple Pay. And for that matter, it’s even more limited than you think. Apple’s choice to leave the Passbook driven Apple Pay experience as threadbare as possible seems an intentional choice to force consumers to interact more with their bank apps vs Passbook for all and any rich interaction. Infact the transaction detail displayed on the back of the payment card you use is limited – but you can launch the bank app to view and do a lot more. Similarly – the bank app can prompt a transaction alert that the consumer can select to view more detail as well. Counter to what has been publicized – Apple can – if they choose to – view transaction detail including consumer info, but only retains anonymized info on their servers. The contrast is apparent with Google – where (during early Google Wallet days) issuers dangled the same anonymized transaction info to appease Google – in return for participation in the wallet. If your tap don’t work – will you blame Apple? Some claim that any transaction failures – such as a non-working reader – will cause consumers to blame Apple. This does not hold water simply because – Apple does not get in between the consumer, his chosen card and the merchant during payment. It provides the framework to trigger and communicate a payment credential – and then quietly gets out of the way. This is where Google stumbled – by wanting to become the perennial fly on the wall. And so if for whatever reason the transaction fails, the consumer sees no Apple branding for them to direct their blame. (I draw a contrast later on below with Samsung and LoopPay) Apple Pay is not secure: Laughable and pure FUD. This article references an UBS note talking how Apple Pay is insecure compared to – a pure cloud based solution such as the yet-to-be-launched MCX. This is due to a total misunderstanding of not just Apple Pay – but the hardware/software platform it sits within (and I am not just talking about the benefits of a TouchID, Network Tokenization, Issuer Cryptogram, Secure Element based approach) including, the full weight of security measures that has been baked in to iOS and the underlying hardware that comes together to offer the best container for payments. And against all that backdrop of applied cryptography, Apple still sought to overlay its payments approach over an existing framework. So that, when it comes to risk – it leans away from the consumer and towards a bank that understands how to manage risk. That’s the biggest disparity between these two approaches – Apple Pay and MCX – that, Apple built a secure wrapper around an existing payments hierarchy and the latter seeks to disrupt that status quo. Let the games begin: Consumers should get ready for an ad blitz from each of the launch partners of Apple Pay over the next few weeks. I expect we will also see these efforts concentrated around pockets of activation – because setting up Apple Pay is the next step to entering your Apple ID during activation. And for that reason – each of those launch partners understand the importance of reminding consumers why their card should be top of mind. There is also a subtle but important difference between top of wallet card (or default card) for payment in Apple Pay and it’s predecessors (Google Wallet for example). Changing your default card was an easy task – and wholly encapsulated – within the Google Wallet app. Where as in Apple Pay – changing your default card – is buried under Settings, and I doubt once you choose your default card – you are more likely to not bother with it. And here’s how quick the payment interaction is within Apple Pay (takes under 3 seconds) :- Bring your phone in to proximity of the reader. Screen turns on. Passbook is triggered and your default card is displayed. You place your finger and authenticate using TouchID. A beep notes the transaction is completed. You can flip the card to view a limited transaction detail. Yes – you could swipe down and choose another card to pay. But unlikely. I remember how LevelUp used very much the same strategy to signup banks – stating that over 90% of it’s customers never change their default card inside LevelUp. This will be a blatant land grab over the next few months – as tens of millions of new iPhones are activated. According to what Apple has told it’s launch partners – they do expect over 95% of activations to add at least one card. What does this mean to banks who won’t be ready in 2014 or haven’t yet signed up? As I said before – there will be a long tail of reduced utility – as we get in to community banks and credit unions. The risk is amplified because Apple Pay is the only way to enable payments in iOS that uses Apple’s secure infrastructure – and using NFC. For those still debating whether it was a shotgun wedding, Apple’s approach had five main highlights that appealed to a Bank – Utilizing an approach that was bank friendly (and to status quo) : NFC Securing the transaction beyond the prerequisites of EMV contactless – via network tokenization & TouchID Apple’s preference to stay entirely as an enabler – facilitating a secure container infrastructure to host bank issued credentials. Compressing the stack: further shortening the payment authorization required of the consumer by removing the need for PIN entry, and not introducing any new parties in to the transaction flow that could have introduced delays, costs or complexity in the roundtrip. Clear description of costs to participate – Free is ambiguous. Free leads to much angst as to what the true cost of participation really is(Remember Google Wallet?). Banks prefer clarity here – even if it means 15bps in credit. As I wrote above, Apple opting to strictly coloring inside the lines – forces the banks to shoulder much of the responsibility in dealing with the ‘before’ and ‘after’ of payment. Most of the bank partners will be updating or activating parts of their mobile app to start interacting with Passbook/Apple Pay. Much of that interaction will use existing hooks in to Passbook – and provide richer transaction detail and context within the app. This is an area of differentiation for the future – because those banks who lack the investment, talent and commitment to build a redeeming mobile services approach will struggle to differentiate on retail footprint alone. And as smarter banks build entirely digital products for an entirely digital audience – the generic approaches will struggle and I expect at some point – that this will drive bank consolidation at the low end. On the other hand – if you are an issuer, the ‘before’ and ‘after’ of payments that you are able to control and the richer story you are able to weave, along with offline incentives – can aid in recapture. The conspicuous and continued absence of Google: So whither Android? Uniformity in payments for Android is as fragmented as the ecosystem itself. Android must now look at Apple for lessons in consistency. For example, how Apple uses the same payment credential that is stored in the Secure Element for both in-person retail transactions as well as in-app payments. It may look trivial – but when you consider that Apple came dangerously close (and justified as well) in its attempt to obtain parity between those two payment scenarios from a rate economics point of view from issuers – Android flailing around without a coherent strategy is inexcusable. I will say this again: Google Wallet requires a reboot. And word from within Google is that a reboot may not imply a singular or even a cohesive approach. Google needs to swallow its pride and look to converge the Android payments and commerce experience across channels similar to iOS. Any delay or inaction risks a growing apathy from merchants who must decide what platform is worth building or focusing for. Risk vs Reward is already skewed in favor of iOS: Even if Apple was not convincing enough in its attempt to ask for Card Present rates for its in-app transactions – it may have managed to shift liability to the issuer similar to 3DS and VBV – that in itself poses an imbalance in favor of iOS. For a retail app in iOS – there is now an incentive to utilize Apple Pay and iOS instead of all the other competing payment providers (Paypal for example, or Google Wallet) because transactional risk shifts to the issuer if my consumer authenticates via TouchID and uses a card stored in Apple Pay. I have now both an incentive to prefer iOS over Android as well as an opportunity to compress my funnel – much of my imperative to collect data during the purchase was an attempt to quantify for fraud risk – and the need for that goes out of the window if the customer chooses Apple Pay. This is huge and the repercussions go beyond Android – in to CNP fraud, CRM and loyalty. Networks, Tokens and new end-points (e.g. LoopPay): The absence of uniformity in Android has provided a window of opportunity for others – regardless of how fragmented these approaches be. Networks shall parlay the success with tokenization in Apple Pay in to Android as well, soon. Prime example being: Loop Pay. If as rumors go – Samsung goes through with baking in Loop Pay in to its flagship S6, and Visa’s investment translates in to Loop using Visa tokenization – Loop may find the ubiquity it is looking for – on both ends. I don’t necessarily see the value accrued to Samsung for launching a risky play here: specifically because of the impact of putting Loop’s circuitry within S6. Any transaction failure in this case – will be attributed to Samsung, not to Loop, or the merchant, or the bank. That’s a risky move – and I hope – a well thought out one. I have some thoughts on how the Visa tokenization approach may solve for some of the challenges that Loop Pay face on merchant EMV terminals – and I will share those later. The return of the comeback: Reliance on networks for tokenization does allay some of the challenges faced by payment wrappers like Loop, Coin etc – but they all focus on the last mile and tokenization does little more for them than kicking the can down the road and delaying the inevitable a little while more. The ones that benefit most are the networks themselves – who now has wide acceptance of their tokenization service – with themselves firmly entrenched in the middle. Even though the EMVCo tokenization standard made no assumptions regarding the role of a Token Service Provider – and in fact Issuers or 3rd parties could each pay the role sufficiently well – networks have left no room for ambiguity here. With their role as a TSP – networks have more to gain from legitimizing more end points than ever before – because these translate to more token traffic and subsequently incremental revenue – transactional and additional managed services costs (OBO – On behalf of service costs incurred by a card issuer or wallet provider). It has never been a better time to be a network. I must say – a whiplash effect for all of us – who called for their demise with the Chase-VisaNet deal. So my predictions for Apple Pay a week before its launch: We will see a substantial take-up and provisioning of cards in to Passbook over the next year. Easy in-app purchases will act as the carrot for consumers. Apple Pay will be a quick affair at the point-of-sale: When I tried it few weeks ago – it took all of 3 seconds. A comparable swipe with a PIN (which is what Apple Pay equates to) took up to 10. A dip with an EMV card took 23 seconds on a good day. I am sure this is not the last time we will be measuring things. The substantial take-up on in-app transactions will drive signups: Consumers will signup because Apple’s array of in-app partners will include the likes of Delta – and any airline that shortens the whole ticket buying experience to a simple TouchID authentication has my money. Apple Pay will cause MCX to fragment: Even though I expect the initial take up to be driven more on the in-app side vs in-store, as more merchants switch to Apple Pay for in-app, consumers will expect a consistency in that approach across those merchants. We will see some high profile desertions – driven partly due to the fact that MCX asks for absolute fealty from its constituents, and in a rapidly changing and converging commerce landscape – that’s just a tall ask. In the near-term, Android will stumble: Question is if Google can reclaim and steady its own strategy. Or will it spin off another costly experiment in chasing commerce and payments. The former will require it to be pragmatic and bring ecosystem capabilities up to par – and that’s a tall ask when you lack the capacity for vertical integration that Apple has. And from the looks of it – Samsung is all over the place at the moment. Again – not confidence inducing. ISIS/SoftCard will get squeezed out of breath: SoftCard and GSMA can’t help but insert themselves in to the Apple Pay narrative by hoping that the existence of a second NFC controller on the iPhone6 validates/favors their SIM based Secure Element approach and indirectly offers Softcard/GSMA constituents a pathway to Apple Pay. If that didn’t make a lick of sense – It’s like saying ‘I’m happy about my neighbor’s Tesla because he plugs it in to my electric socket’. Discover how an Experian business consultant can help you strengthen your credit and risk management strategies and processes: http://ex.pn/DA_GCP This post originally appeared here.
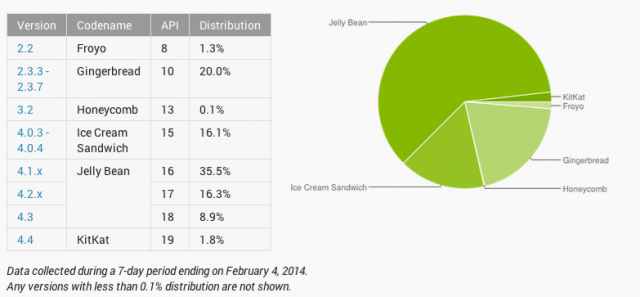
Both Visa and MasterCard announced their support for Host Card Emulation (HCE) and their intent to release HCE specifications soon. I have been talking about HCE from late 2012 (partly due to my involvement with SimplyTapp) and you could read as to why HCE matter and what Android KitKat-HCE announcement meant for payments. But in light of the network certification announcements yesterday, this post is an attempt to provide some perspective on what the Visa/MasterCard moves mean, how do their approaches differ in certifying payments using cloud hosted credentials, what should issuers expect from a device and terminal support perspective, why retailers should take note of the debate around HCE and ultimately – the role I expect Google to continue to play around HCE. All good stuff. First, what do the Visa/MasterCard announcements mean? It means that it’s time for banks and other issuers to stop looking for directions. The network announcements around HCE specifications provide the clarity required by issuers to meaningfully invest in mobile contactless provisioning and payment. Further, it removes some of the unfavorable economics inherited from a secure element-centric model, who were forced to default to credit cards with higher interchange in the wallet. Renting space on the secure element cost a pretty penny and that is without taking operational costs in to consideration, and as an issuer if you are starting in the red out of the gate, you were not about to put a Durbin controlled debit card in the wallet. But those compulsions go with the wind now, as you are no longer weighed down by these costs and complexities on day one. And further, the door is open for retailers with private label programs or gift cards to also look at this route with a lot more interest. And they are. MasterCard mentioned bank pilots around HCE in its press release, but MCX is hardly the only retailer payment initiative in town. Let me leave it at that. How do the Visa/MasterCard specs differ? From the press releases, some of those differences are evident – but I believe they will coalesce at some point in the future. MasterCard’s approach speaks to mobile contact-less as the only payment modality, whereas Visa refers to augmenting the PayWave standard with QR and in-app payments in the future. Both approaches refer to payment tokens (single or multi-use) and one can expect them to work together with cloud provisioned card profiles, to secure the payment transaction and verify transactional integrity. To MasterCard’s benefit – it has given much thought to ensuring that these steps – provisioning the card profile, issuing payment tokens et al – are invisible to the consumer and therefore refrains from adding undue friction. I am a purist at heart – and I go back to the first iteration of Google Wallet – where all I had to do to pay was turn on the screen and place the device on the till. That is the simplicity to beat for any issuer or retailer payment experiences when using contactless. Otherwise, they are better off ripping out the point-of-sale altogether. MasterCard’s details also makes a reference to a PIN. The PIN will not be verified offline as it would have been if a Secure Element would have been present in the device, rather – it would be verified online which tells me that an incorrect PIN if input would be used to create an “incorrect cryptogram” which would be rejected upstream. Now I am conflicted using a PIN at the point of sale for anything – to me it is but a Band-Aid, it reflects the inability to reduce fraud without introducing friction. Visa so far seems to be intentionally light on details around mandating a PIN, and I believe not forcing one would be the correct approach – as you wouldn’t want to constrain issuers to entering a PIN as means to do authentication, and instead should have laid down the requirements but left it to the market to decide what would suffice – PIN, biometrics et al. Again – I hope these specs will continue to evolve and move towards a more amenable view towards customer authentication. Where do we stand with device and terminal support? All of this is mute if there are not enough devices that support NFC and specifically – Android KitKat. But if you consider Samsung devices by themselves (which is all one should consider for Android) they control over 30% of the NA market – 44.1 million devices sold in 2013 alone. Lion share of those devices support NFC out of the box – including Galaxy Note II and 3, Galaxy S3 and S4 – and their variants mini, Active, Xoom et al. And still, the disparity in their approach to secure elements, continuing lack of availability in standards and Android support – Tap and Pay was largely a dream. What was also worrisome is that 3 months after the launch of Android KitKat – it still struggles under 2% in device distribution. That being said, things are expected to get markedly better for Samsung devices at least. Samsung has noted that 14 of its newer devices will receive KitKat. These devices include all the NFC phones I have listed above. Carriers must follow through quickly (tongue firmly in cheek) to deliver on this promise before customers with old S3 devices see their contracts expire and move to a competitor (iPhone 6?). Though there was always speculation as to whether an MNO will reject HCE as part of the Android distribution, I see that as highly unlikely. Even carriers know a dead horse when they see one, and Isis’s current model is anything but one. Maybe Isis will move to embrace HCE. And then there is the issue of merchant terminals. When a large block of merchants are invested in upending the role of networks in the payment value chain – that intent ripples far and wide in the payments ecosystem. Though it’s a given that merchants of all sizes can expect to re-terminalize in the next couple of years to chip & pin (with contactless under the hood) – it is still the prerogative of the merchant as to whether the contactless capability is left turned on or off. And if merchants toe Best Buy’s strategy in how it opted to turn it off store-wide, then that limits the utility of an NFC wallet. And why wouldn’t they? Merchants have always viewed “Accept all cards” to also mean “Accept all cards despite the form factor” and believes that contactless could come to occupy a higher interchange tier in the future – as questions around fraud risk are sufficiently answered by the device in real-time. This fear is though largely unsubstantiated, as networks have not indicated that they could come to view mobile contact-less as being a “Card Present Plus” category that charges more. But in the absence of any real assurances, fear, uncertainty and doubt runs rampant. But what could a retailer do with HCE? If re-terminalization is certain, then retailers could do much to explore how to leverage it to close the gap with their customer. Private label credit, closed loop are viable alternatives that can be now carried over contactless – and if previously retailers were cut out of the equation due to heavy costs and complexity for provisioning cards to phones, they have none of those limitations now. A merchant could now fold in a closed loop product (like a gift card) in to their mobile app – and accept those payments over contact-less without resorting to clunky QR or barcode schemes. There is a lot of potential in the closed loop space with HCE, that Retailers are ignoring due to a “scorched earth” approach towards contactless. But smarter merchants are asking ‘how’. Finally, what about Google? Google deserves much praise for finally including HCE in Android and paving the way for brands to recognize the opportunity and certify the approach. That being said, Google has no unequal advantage with HCE. In fact, Google has little to do with HCE going forward, despite GoogleWallet utilization of HCE in the future. I would say – HCE has as much to do with Google going forward, as Amazon’s Kindle Fire has to do with Android. Banks and Retailers have to now decide what this means for them – and view HCE as separate to Google – and embrace it if they believe it has potential to incent their brands to remain top of wallet, and top of mind for the consumer. It is a level playing field, finally. Where do you go next? Indeed – there is a lot to take in – starting with HCE’s role, where it fit in to your payment strategy, impact and differences in Visa/MasterCard approaches, weaving all of these in to your mobile assets while not compromising on customer experience. Clarity and context is key and we can help with both. Reach out to us for a conversation. HCE is a means to an end – freeing you from the costs and complexities of leveraging contactless infrastructure to deliver an end-to-end mobile experience, but there is still the question of how your business should evolve to cater to the needs of your customers in the mobile channel. Payment is after all, just one piece of the puzzle.

By: Teri Tassara In my blog last month, I covered the importance of using quality credit attributes to gain greater accuracy in risk models. Credit attributes are also powerful in strengthening the decision process by providing granular views on consumers based on unique behavior characteristics. Effective uses include segmentation, overlay to scores and policy definition – across the entire customer lifecycle, from prospecting to collections and recovery. Overlay to scores – Credit attributes can be used to effectively segment generic scores to arrive at refined “Yes” or “No” decisions. In essence, this is customization without the added time and expense of custom model development. By overlaying attributes to scores, you can further segment the scored population to achieve appreciable lift over and above the use of a score alone. Segmentation – Once you made your “Yes” or “No” decision based on a specific score or within a score range, credit attributes can be used to tailor your final decision based on the “who”, “what” and “why”. For instance, you have two consumers with the same score. Credit attributes will tell you that Consumer A has a total credit limit of $25K and a BTL of 8%; Consumer B has a total credit limit of $15K, but a BTL of 25%. This insight will allow you to determine the best offer for each consumer. Policy definition - Policy rules can be applied first to get the desirable universe. For example, an auto lender may have a strict policy against giving credit to anyone with a repossession in the past, regardless of the consumer’s current risk score. High quality attributes can play a significant role in the overall decision making process, and its expansive usage across the customer lifecycle adds greater flexibility which translates to faster speed to market. In today’s dynamic market, credit attributes that are continuously aligned with market trends and purposed across various analytical are essential to delivering better decisions.
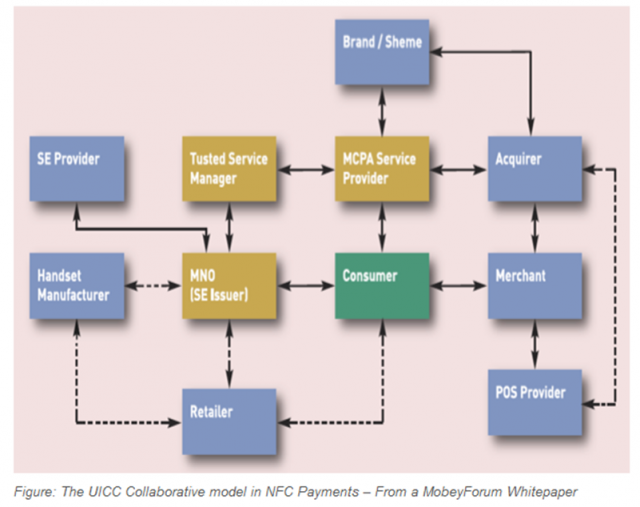
When I wrote about Host Card Emulation back in March, it provoked much debate around whether this capability will die on the cutting floor or be meaningfully integrated in to a future Android iteration. And now that it has, this post is an attempt to look forward, even though much of it is speculative. But I will provide some perspective from a number of conversations I had in the last week with Networks, Issuers, TSMs, Merchants, Platform Owners and EMV practitioners and provide some insight in to perceptions, impacts and the road ahead for NFC. And I will provide some context to why HCE matters to each of these players. First – if you haven’t read my previous post on HCE – this would be a good time to do so. Media has unfortunately focused yet again on the controversy in light of the KitKat HCE announcement – focusing on the end-run around Carriers rather than the upside this brings to those who have been disincentivized previously to consider NFC. What they all seem to have missed is that HCE allows for the following: it reduces the gap between merchants and card issuance, brings the topic of closed-loop and contactless in focus, and more tactically – allows for an easy deployment scenario that does not require them to change the software inside the terminal. I hope those three things do not get lost in translation. Google: Being a Platform Owner for once The Android team deserves much credit for enabling support for Host Card Emulation in KitKat. Beyond the case for platform support – something Blackberry already had – there were both altruistic and selfish reasons for going this route. The former – altruistic – had to do with throwing open another door that would invite third party developers to build on an open NFC stack – while firmly shutting other ones (read criticism from Ars that Android is quickly becoming a closed source – partly through its Play services approach). It was time it acted like a platform owner. And being one entailed democratizing access to tap-and-pay. Selfish – because for the more than 200M Android devices that shipped with NFC support – a fraction of these are tap-and-pay worthy. It had become absurd that one must enquire upon Carrier, Platform, Issuer and Device support before installing an NFC payment app, much less use it. Talk about fragmentation. This was a problem only Google could begin to fix – by removing the absurd limitations put in place in the name of security – but in truth existed because of profit, control and convenience. Google’s role hardly ends here. Today – Host Card Emulation – by definition alone, is reserved as a technical topic. Out of the gate, much needs to be done to educate Issuers and Merchants as to why this matters. For retailers – used to much cynicism in matters relating to NFC – Host Card Emulation offers an opportunity to develop and deploy a closed-loop contactless scheme using retailer’s preferred payment sources – private label, debit, credit and in that order. HCE to Merchants: Friend or Foe? In my opinion – merchants stand to benefit most from HCE. Which is another reason why Google really embraced this concept. Despite having certain benefits for Issuers to provision cards without having to pay the piper, Google had its eyes set on expanding the offline footprint for GoogleWallet and to successfully do so – needed to focus on the merchant value prop while dialing back on what retailers once called the “data donation agreement”. Where merchants primarily struggle today in mobile – is not in replicating the plastic model – it is to create a brand new loyalty platform where the customer sets a payment source and forgets it – preferably one that’s preferred by the merchant – for example a private label card or debit. Except, no open loop wallets had actually centered itself around this premise so far. Google Wallet launched with Citi, then reverted to a negative margin strategy – by charging the merchant CP rates while paying the Issuers CNP rates. It wasn’t ideal – as merchants did not want Google anywhere near the transaction value chain. Meanwhile – it gave Google quite the heartburn to see Apple being successful with Passbook – requiring merchants give nothing back in return for leveraging it to deliver geo-targeted offers and loyalty. This silent takedown must have forced Google’s hands in getting serious about building a complete offer, loyalty, payment scheme that is collaborative (HCE support was a collaborative effort introduced by SimplyTapp) and merchant friendly. I believe HCE support now represents a serious effort to help merchants commercialize a closed-loop advantage in contactless without requiring software changes inside the terminal. Contactless was out of bounds for merchants till now. Not anymore. Having fielded a number of calls from retailers as to what this means, I will distill retailer reactions down to this: measured optimism, casual pessimism and “network” cynicism. Retailers have always looked at EMV and terminalization as a head-fake for NFC – to further lay down the tracks for another three decades of control around pricing and what they see as anti-competitive behavior. Though HCE is in no way tethered to NFC (it’s agnostic of a communication method) – due to its current close association with NFC, merchants see the conversation as a non-starter – until there is a constructive dialogue with networks. At the same time, merchants are cautiously optimistic about the future of HCE – provided that there is a standards body that provides them equal footing with Platform owners, Issuers and networks – to dictate its scope and future. As the platform owner – Google should work with the merchant body, networks, issuers and other stakeholders to see this through. It was not a surprise that those who I talked to all agreed about one thing: that Carriers really should have no role to play in this framework. TSM’s/SE Providers: Where to from here? The nine party model is dead, or will be very soon – as the SE rental model has been shown as previously not being sustainable – and now with HCE – simply wasteful. TSM’s had been focused outside of US for the last several years – as the lack of meaningful commercial launches meant that the US market will simply not bring scale for many years. And with Google shifting away from using a Secure Element in its flagship Nexus models – the writing was already on the wall. TSM’s will look to extend their capabilities in to non-traditional partnerships (Gemalto/MCX) and in to non-hardware scenarios (competing with Cloud SE providers like SimplyTapp in the HCE model). Bell-ID is such an example – and quite likely the only example right now. Networks: Certify or Not? What does Host Card Emulation mean to V/MA? It is no secret that the networks had more than toyed with the idea of software card emulation these last couple of years – realizing the rapidly shrinking runway for NFC. Focus for networks should be now to certify the new approach, as a legitimate way to store and transfer credentials. It’s interesting to hear how our neighbors in the north have reacted to this news. There is still ambiguity among Canadian issuers and networks as to what this means – including debates as to whether an onboard SE is still required for secure storage. That ambiguity will not dissipate till V/MA step in and do their part. I must quote an EMV payments consultant from the north who wrote to me this week: “My boss calls the TSM model “traditional” and I remind him in NFC payments there is no tradition… I think for some people the Global Platform standards with the TSM smack in the middle are like a comfort food – you know what you are getting and it feels secure (with 1000′s of pages of documentation how could they not be!)” That should give GP and TSMs some comfort. Device Support for HCE: What does that look like? Google does not report sales figures on Nexus 4, Nexus 5, Google Play editions of Samsung Galaxy S4 and HTC One – the four devices that are slated to receive KitKat over the next few weeks (apart from the Nexus tablets). So if I would venture a guess – I would say approx 20M devices in total that has NFC capability that will support Host Card Emulation soon. That may not seem much – but it’s a strong base . There is also a possibility that post-Galaxy Nexus devices from Samsung may leapfrog 4.3 to go directly to KitKat. If that happens – just based on reported sales volumes for Galaxy S3 and S4 – that would be a total of 100M devices with NFC support. What does that mean for Samsung’s revenue model around SE – who has an embedded SE from Oberthur in the S3 & S4 devices, which it hopes to charge rent to Visa and others – that’s unclear at this point. Issuers: ISIS alternative or more? For those issuers who passed on Isis, or those who were scorned by Isis – this enables them to outfit their current mobile assets with a payment feature. I wrote about the absurdity in a contactless transaction where the consumer has to close his merchant or banking app and switch to Isis to tap-and-pay – instead of equipping merchant/bank apps with a tap-and-pay feature. HCE means a lot more for Private label Issuers – who have a very inspired base of merchants looking to bridge the gap between private label cards and mobile – and now have an alternative to clumsy, costly and complex orchestrations for provisioning cards – replaced with an easy integration and cheaper deployment. More about that later. Finally, Carriers & Isis: Fight or Flight? God Speed.
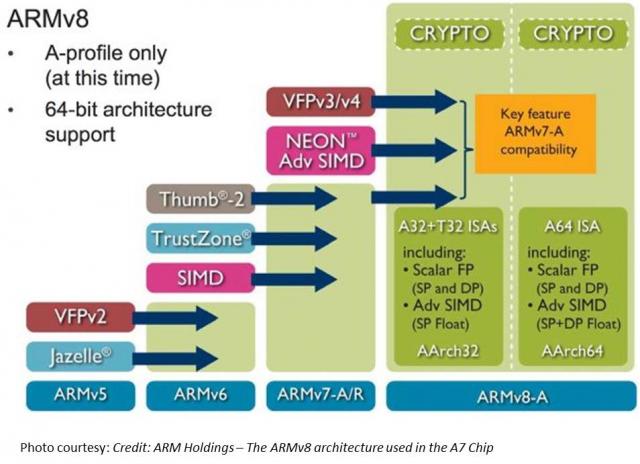
TL;DR Read within as to how Touch ID is made possible via ARM’s TrustZone/TEE, and why this matters in the context of the coming Apple’s identity framework. Also I explain why primary/co-processor combos are here to stay. I believe that eventually, Touch ID has a payments angle – but focusing on e-commerce before retail. Carriers will weep over a lost opportunity while through Touch ID, we have front row seats to Apple’s enterprise strategy, its payment strategy and beyond all – the future direction of its computing platform. I had shared my take on a possible Apple Biometric solution during the Jan of this year based on its Authentec acquisition. I came pretty close, except for the suggestion that NFC is likely to be included. (Sigh.) Its a bit early to play fast and loose with Apple predictions, but its Authentec acquisition should rear its head sometime in the near future (2013 – considering Apple’s manufacturing lead times), that a biometric solution packaged neatly with an NFC chip and secure element could address three factors that has held back customer adoption of biometrics: Ubiquity of readers, Issues around secure local storage and retrieval of biometric data, Standardization in accessing and communicating said data. An on-chip secure solution to store biometric data – in the phone’s secure element can address qualms around a central database of biometric data open to all sorts of malicious attacks. Standard methods to store and retrieve credentials stored in the SE will apply here as well. Why didn’t Apple open up Touch ID to third party dev? Apple expects a short bumpy climb ahead for Touch ID before it stabilizes, as early users begin to use it. By keeping its use limited to authenticating to the device, and to iTunes – it can tightly control the potential issues as they arise. If Touch ID launched with third party apps and were buggy, it’s likely that customers will be confused where to report issues and who to blame. That’s not to say that it won’t open up Touch ID outside of Apple. I believe it will provide fettered access based on the type of app and the type of action that follows user authentication. Banking, Payment, Productivity, Social sharing and Shopping apps should come first. Your fart apps? Probably never. Apple could also allow users to set their preferences (for app categories, based on user’s current location etc.) such that biometrics is how one authenticates for transactions with risk vs not requiring it. If you are at home and buying an app for a buck – don’t ask to authenticate. But if you were initiating a money transfer – then you would. Even better – pair biometrics with your pin for better security. Chip and Pin? So passé. Digital Signatures, iPads and the DRM 2.0: It won’t be long before an iPad shows up in the wild sporting Touch ID. And with Blackberry’s much awaited and celebrated demise in the enterprise, Apple will be waiting on the sidelines – now with capabilities that allow digital signatures to become ubiquitous and simple – on email, contracts or anything worth putting a signature on. Apple has already made its iWork productivity apps(Pages, Numbers, Keynote), iMovie and iPhoto free for new iOS devices activated w/ iOS7. Apple, with a core fan base that includes photographers, designers and other creative types, can now further enable iPads and iPhones to become content creation devices, with the ability to attribute any digital content back to its creator by a set of biometric keys. Imagine a new way to digitally create and sign content, to freely share, without worrying about attribution. Further Apple’s existing DRM frameworks are strengthened with the ability to tag digital content that you download with your own set of biometric keys. Forget disallowing sharing content – Apple now has a way to create a secondary marketplace for its customers to resell or loan digital content, and drive incremental revenue for itself and content owners. Conclaves blowing smoke: In a day and age where we forego the device for storing credentials – whether it be due to convenience or ease of implementation – Apple opted for an on-device answer for where to store user’s biometric keys. There is a reason why it opted to do so – other than the obvious brouhaha that would have resulted if it chose to store these keys on the cloud. Keys inside the device. Signed content on the cloud. Best of both worlds. Biometric keys need to be held locally, so that authentication requires no roundtrip and therefore imposes no latency. Apple would have chosen local storage (ARM’s SecurCore) as a matter of customer experience, and what would happen if the customer was out-of-pocket with no internet access. There is also the obvious question that a centralized biometric keystore will be on the crosshairs of every malicious entity. By decentralizing it, Apple made it infinitely more difficult to scale an attack or potential vulnerability. More than the A7, the trojan in Apple’s announcement was the M7 chip – referred to as the motion co-processor. I believe the M7 chip does more than just measuring motion data. M7 – A security co-processor? I am positing that Apple is using ARM’s TrustZone foundation and it may be using the A7 or the new M7 co-processor for storing these keys and handling the secure backend processing required. Horace Dediu of Asymco had called to question why Apple had opted for M7 and suggested that it may have a yet un-stated use. I believe M7 is not just a motion co-processor, it is also a security co-processor. I am guessing M7 is based on the Cortex-M series processors and offloads much of this secure backend logic from the primary A7 processor and it may be that the keys themselves are likely to be stored here on M7. The Cortex-M4 chip has capabilities that sound very similar to what Apple announced around M7 – such as very low power chip, that is built to integrate sensor output and wake up only when something interesting happens. We should know soon. This type of combo – splitting functions to be offloaded to different cores, allows each cores to focus on the function that it’s supposed to performed. I suspect Android will not be far behind in its adoption, where each core focuses on one or more specific layers of the Android software stack. Back at Google I/O 2013, it had announced 3 new APIs (the Fused location provider) that enables location tracking without the traditional heavy battery consumption. Looks to me that Android decoupled it so that we will see processor cores that focus on these functions specifically – soon. I am fairly confident that Apple has opted for ARM’s Trustzone/TEE. Implementation details of the Trustzone are proprietary and therefore not public. Apple could have made revisions to the A7 chip spec and could have co-opted its own. But using the Trustzone/TEE and SecurCore allows Apple to adopt existing standards around accessing and communicating biometric data. Apple is fully aware of the need to mature iOS as a trusted enterprise computing platform – to address the lack of low-end x86 devices that has a hardware security platform tech. And this is a significant step towards that future. What does Touch ID mean to Payments? Apple plans for Touch ID kicks off with iTunes purchase authorizations. Beyond that, as iTunes continue to grow in to a media store behemoth – Touch ID has the potential to drive fraud risk down for Apple – and to further allow it to drive down risk as it batches up payment transactions to reduce interchange exposure. It’s quite likely that à la Walmart, Apple has negotiated rate reductions – but now they can assume more risk on the front-end because they are able to vouch for the authenticity of these transactions. As they say – customer can longer claim the fifth on those late-night weekend drunken purchase binges. Along with payment aggregation, or via iTunes gift cards – Apple has now another mechanism to reduce its interchange and risk exposure. Now – imagine if Apple were to extend this capability beyond iTunes purchases – and allow app developers to process in-app purchases of physical goods or real-world experiences through iTunes in return for better blended rates? (instead of Paypal’s 4% + $0.30). Heck, Apple can opt for short-term lending if they are able to effectively answer the question of identity – as they can with Touch ID. It’s Paypal’s ‘Bill Me Later’ on steroids. Effectively, a company like Apple who has seriously toyed with the idea of a Software-SIM and a “real-time wireless provider marketplace” where carriers bid against each other to provide you voice, messaging and data access for the day – and your phone picks the most optimal carrier, how far is that notion from picking the cheapest rate across networks for funneling your payment transactions? Based on the level of authentication provided or other known attributes – such as merchant type, location, fraud risk, customer payment history – iTunes can select across a variety of payment options to pick the one that is optimal for the app developer and for itself. And finally, who had the most to lose with Apple’s Touch ID? Carriers. I wrote about this before as well, here’s what I wrote then (edited for brevity): Does it mean that Carriers have no meaningful role to play in commerce? Au contraire. They do. But its around fraud and authentication. Its around Identity. … But they seem to be stuck imitating Google in figuring out a play at the front end of the purchase funnel, to become a consumer brand(Isis). The last thing they want to do is leave it to Apple to figure out the “Identity management” question, which the latter seems best equipped to answer by way of scale, the control it exerts in the ecosystem, its vertical integration strategy that allows it to fold in biometrics meaningfully in to its lineup, and to start with its own services to offer customer value. So there had to have been much ‘weeping and moaning and gnashing of the teeth’ on the Carrier fronts with this launch. Carriers have been so focused on carving out a place in payments, that they lost track of what’s important – that once you have solved authentication, payments is nothing but accounting. I didn’t say that. Ross Anderson of Kansas City Fed did. What about NFC? I don’t have a bloody clue. Maybe iPhone6? iPhone This is a re-post from Cherian's original blog post "Smoke is rising from Apple's Conclave"

By: Matt Sifferlen I recently read interesting articles on the Knowledge@Wharton and CNNMoney sites covering the land grab that's taking place among financial services startups that are trying to use a consumer's social media activity and data to make lending decisions. Each of these companies are looking at ways to take the mountains of social media data that sites such as Twitter, Facebook, and LinkedIn generate in order to create new and improved algorithms that will help lenders target potential creditworthy individuals. What are they looking at specifically? Some criteria could be: History of typing in ALL CAPS or all lower case letters Frequent usage of inappropriate comments Number of senior level connections on LinkedIn The quantity of posts containing cats or annoying self-portraits (aka "selfies") Okay, I made that last one up. The point is that these companies are scouring through the data that individuals are creating on social sites and trying to find useful ways to slice and dice it in order to evaluate and target consumers better. On the consumer banking side of the house, there are benefits for tracking down individuals for marketing and collections purposes. A simple search could yield a person's Facebook, Twitter, or LinkedIn profile. The behaviorial information can then be leveraged as a part of more targeted multi-channel and contact strategies. On the commercial banking side, utilizing social site info can help to supplement any traditional underwriting practices. Reviewing the history of a company's reviews on Yelp or Angie's List could share some insight into how a business is perceived and reveal whether there is any meaningful trend in the level of negative feedback being posted or potential growth outlook of the company. There are some challenges involved with leveraging social media data for these purposes. 1. Easily manipulated information 2. Irrelevant information that doesn't represent actual likes, thoughts or relevant behaviors 3. Regulations From a Fraud perspective, most online information can easily and frequently be manipulated which can create a constantly moving target for these providers to monitor and link to the right customer. Fake Facebook and Twitter pages, false connections and referrals on LinkedIn, and fabricated positive online reviews of a business can all be accomplished in a matter of minutes. And commercial fraudsters are likely creating false business social media accounts today for shelf company fraud schemes that they plan on hatching months or years down the road. As B2B review websites continue to make it easier to get customers signed up to use their services, the downside is there will be even more unusable information being created since there are less and less hurdles for commercial fraudsters to clear, particularly for sites that offer their services for free. For now, the larger lenders are more likely to utilize alternative data sources that are third party validated, like rent and utility payment histories, while continuing to rely on tools that can prevent against fraud schemes. It will be interesting to see what new credit and non credit data will be utilized as a common practice in the future as lenders continue their efforts to find more useful data to power their credit and marketing decisions.
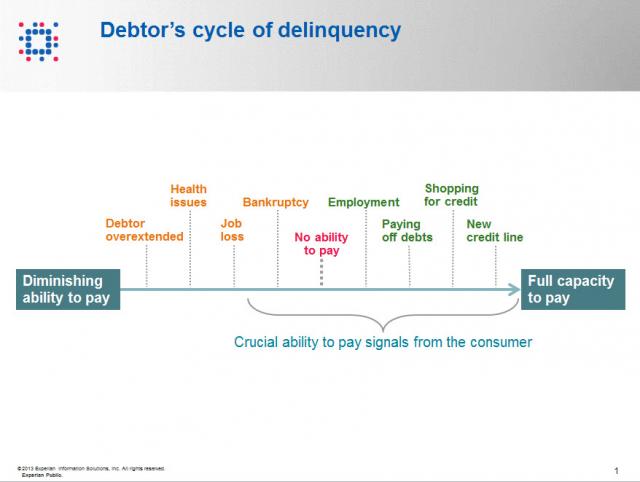
Contact information such as phone numbers and addresses are fundamental to being able to reach a debtor, but knowing when to reach out to the debtor is also a crucial factor impacting success or failure in getting payment. As referenced in the chart below, when a consumer enters the debtor life cycle, they often avoid talking with you about the debt because they do not have the ability to pay. When the debtor begins to recover financially, you want to be sure you are among the first to reach out to them so you can be the first to be paid. According to Don Taylor, President of Automated Collection Services, they have seen a lift of more than 12% of consumers with trigger hits entering repayment, and this on an aged portfolio that has already been actively worked by debt collection staff. Monitoring for a few key changes on the credit profiles of debtors provides the passive monitoring that is needed to tell you the optimal time to reach back to the consumer for payment. Experian compiled several recent collection studies and found that a debtor paying off an account that was previously past due provided a 710% increase in the average payment. Positive improvement on a consumers’ credit profile is one of those vital indicators that the consumer is beginning to recover financially and could have the will—and ability—to pay bad debts. The collection industry is not like the big warehouse stores—quantity and value do not always work hand in hand for the debt collection industry. Targeting the high value credit events that are proven to increase collection amounts is the key to value, and Experian has the expertise, analytics and data to help you collect in the most effective manner. Be sure to check out our other debt collection blog posts to learn how to recover debt more quickly and efficiently.

At midnight yesterday, Google sent me an email on how the new GoogleWallet update will now allow me to store my “Citi MasterCard” online. As other Google Wallet aficionados may recall (Bueller..? Bueller..?), Citi was the lone holdout in Google Wallet’s journey to the cloud and its race to conformity. Though to the untrained eye the Google Wallet app experience was mostly uniform irrespective of the card used to pay at the point-of-sale, behind the scenes, if the Citi MasterCard was used, Google had to do things one way versus another way for the rest of the brood. Furthermore, sharing the precious real estate that is the Secure Element with Citi meant that Google had very little room to maneuver. Embedded SEs, despite being newer to market than SIM-based SE’s, were limited in storage versus other chips. The initial embedded SEs that Google Wallet relied on had about 76KB memory, which once you factor in all the trimmings that come with provisioning a card to SE (MasterCard PayPass applet among others), left very little wiggle room. So Google, forced by a number of factors (resistance from the carriers and issuers, rising costs and complexities attributed to the multiple TSM model, a lack of SE space to accommodate future provisioning) migrated to the cloud — and left a MasterCard proxy on the wallet that it could use to funnel transactions through. The only standout to this model was the umbilical cord to the original Google Wallet partner: Citi. I had predicted last September that the partnership’s days were numbered. When the wallet is Google’s, and it needs to both reclaim the space on SE and reduce the provisioning or account management costs that it owes to its TSM (FirstData), the only reason for it to carry the torch for Citi would be if Google Wallet customers demanded it. But it so happens that any returns for items purchased using Google Wallet untill today had also been slightly broken. If you bought an item using the virtual MasterCard then the returns followed one route; of you purchased an item via the Citi card then returns were handled a different way. Additionally, It was disappointing for a customer to see “Paypass Merchant” instead of “McDonalds” and “Sent” instead of “$25.54″ when paying with the Citi card in GoogleWallet(unless one was planning to hide a fastfood habit from a spouse). A small mess – especially when it should be attributed to powers beyond the partnership, but still a mess for Google who demands conformity in customer experience across all its offerings. In the end, this partnership served no broader purpose for either partner to keep alive for any longer. Google is ready to move on beyond Wallet 1.0 and realizes that it can do so without issuers in tow. Furthermore, it had been expected for a better part of three months that Google will launch its partnership with Discover and this puts Google as an indispensable element back in the mobile payment narrative. For the issuers who were originally courted by Google Wallet in its early days this serves as validation, that they were correct in choosing to stay away. But that is no excuse for ignoring what Google and others are building as a parallel framework to the value-added services (credit card rewards being one) card issuers use to show that customers will choose them over Google. (But if Google could tout interchange relief to merchants as an incentive to court them, don’t you think a Google Rewards program will be close behind, supported by credits redeemable the Google Play store? Once again, it’s not an if, but when.) Finally, where does this leave Citi? Citi is a global institution with enough smart people at their end to make up for lost time. Google Wallet did not become the boogeyman that issuers feared back in 2011, and Citi can afford to roll out its own mobile initiatives in a measured pace at a global scale. And there had been rumblings of a Citi wallet all through 2012 and we may see it soon manifest outside of the U.S. before Citi attempts to do so here. Google may have opted to cut the cord so that there is no ambiguity when that happens. But they still have both Citi and FirstData to thank for bringing it to the prom. You dance with the one that brung ya…or something like it. Do you think this means GoogleWallet is now adrift, loyal to its own quest? What’s next for Citi? What do you think? Please leave your opinions below. This is a re-post from Cherian's personal blog at DropLabs

First, it aims to drastically reduce payment acceptance costs through any and all means and Secondly – keep merchant data firmly within their purview. MCX – MerChants reduX: The post that follows is a collection of thoughts around MCX, why it deserves respect, and yet how it is indeed mortal and bleeds like all others. For those who are not familiar with MCX – it’s a consortium of over 30 leading national retailers with a singular purpose – that is, to create a seamlessly integrated mobile commerce platform. The website for MCX is http://www.mcx.com. The consortium is led by merchants like Walmart, Target, CVS, BestBuy, Gap, Sears etc. By 2012, the mobile payments space was fragmented as it is, which itself may have precipitated the launch of MCX. And to a number of solutions looking for traction, things ground to a halt when MCX conceptualized to the merchants a solution that needed no costly upgrades and a promise to route the transaction over low cost routing options. My friends on the issuer side privately confide that MCX has infact succeeded in throwing a monkey wrench in their mobile payment plans – and merchant acceptance looks to be ambiguous around incumbent initiatives such as Isis and GoogleWallet, as well as for alternative payment initiatives. It had been easy to call it mere posturing and ignore it in the early days, but of late there is a lot of hand wringing behind the scenes and too many furrowed brows, as if the realization finally struck that merchants were indeed once again crucial to mobile payment adoption. MCX – It’s raison d’etre Meanwhile, the stakeholders behind MCX have been religious in their affirmation that MCX lives by two core tenets: First, it aims to drastically reduce payment acceptance costs through any and all means and Secondly – keep merchant data firmly within their purview. I can’t seem to think that the latter was any more than an after thought, because merchants individually can choose to decide if they wish to share customer preferences or Level III data with third parties, but they need all the collective clout they can muster to push networks and issuers to agree to reduce card acceptance costs. So if one distils MCX down to its raison d’etre, then it looks that it is aimed squarely at No.1. Which is fair when you consider that the merchants believe card fees are one of their biggest operating expenses. In 2007, 146,000 convenience stores and gas stations nationwide made a total of $3.4B in profits, yet they paid out $7.6B in card acceptance costs(Link). And MCX is smart to talk about the value of merchant data, the need to control it, yada yada yada. But if that were indeed more important, Isis could have been the partner of choice – someone who would treat customer and transaction data as sacrosanct and leave it behind for the merchants to fiddle with(vs. GoogleWallet’s mine..mine..mine.. strategy). But the same way HomeDepot was disappointed when they first saw GoogleWallet – no interchange relief, incremental benefits at the point-of-sale, and swoops all their data in return, Isis also offers little relief to MCX or its merchants, even without requiring any transaction or SKU level data in return. Does it mean that Carriers have no meaningful role to play in commerce? Au contraire. They do. But its around fraud and authentication. Its around Identity. And creating a platform for merchants to deliver coupons, alerts to opted-in customers. But they seem to be stuck imitating Google in figuring out a play at the front end of the purchase funnel, to become a consumer brand. The last thing they want to do is leave it to Apple to figure out the “Identity management” question, which the latter seems best equipped to answer by way of scale, the control it exerts in the ecosystem, its vertical integration strategy that allows it to fold in biometrics meaningfully in to its lineup, and to start with its own services to offer customer value. Did we say Apple? Its a bit early to play fast and loose with Apple predictions, but its Authentec acquisition should rear its head sometime in the near future (2013 – considering Apple’s manufacturing lead times), that a biometric solution packaged neatly with an NFC chip and secure element could address three factors that has held back customer adoption of biometrics: Ubiquity of readers, Issues around secure local storage and retrieval of biometric data, Standardization in accessing and communicating said data. An on-chip secure solution to store biometric data – in the phone’s secure element can address qualms around a central database of biometric data open to all sorts of malicious attacks. Standard methods to store and retrieve credentials stored in the SE will apply here as well. Why NFC? If NFC was originally meant to seamlessly and securely share content, what better way to sign that content, to have it be attributable to its original author, or to enforce one’s rights to said content – than to sign it with one’s digital signature. Identity is key, not just when enforcing digital rights management on shared content, but also to secure commerce and address payment/fraud risk. Back to MCX. The more I read the more it seems MCX is trying to imitate Isis in competing for the customer mindshare, in attempting to become a consumer brand – than simply trying to be a cheaper platform for payment transactions. As commerce evolved beyond being able to be cleanly classified under “Card Present” and “Card Not Present” – as transactions originate online but get fulfilled in stores, merchants expect rules to evolve alongside reality. For example, when customers are able to order online, but pick up in-store after showing a picture ID, why would merchants have to pay “Card not Present” rates when risk is what we attribute higher CNP rates to, and why is there an expectation of the same amount of risk even in this changed scenario? And beyond, as technology innovation blurs the lines that neatly categorized commerce, where we replace “Card Present” with “Mobile Present”, and mobile carry a significant amount of additional context that could be scored to address or quantify risk, why shouldn’t it be?. It’s a given that networks will have to accommodate for reduced risk in transactions where mobile plays a role, where the merchant or the platform enabling the transaction can meaningfully use that context to validate customer presence at the point-of-sale – and that they will expect appropriate interchange reduction in those scenarios. MCX – A brand like Isis or a platform? But when reading portions of the linked NRF blog, and elsewhere – it reflects a misplaced desire on MCX’s part to become a consumer facing solution – an app that all MCX partners will embrace for payment. This is so much like the Isis solution of today – that I have written about – and why it flies in the face of reason. Isis – the nexus between Carriers and FI’s – is a powerful notion, if one considers the role it could play in enabling an open platform – around provisioning, authentication and marketing. But for that future to materialize, Isis has to stop competing with Google, and must accept that it has little role to play by itself at the front end of the funnel, and must recede to its role of an enabler – one that puts its partner FI brands front and center, allows Chase’s customers to pay using Chase’s mobile app instead of Isis, and drives down the fraud risk at the point of sale by meaningfully authenticating the customer via his location and mobile assets Carriers control, and further – the historical data they have on the customer. It’s those three points of data and the scale Isis can bring, that puts them credibly in the payments value chain – not the evaporating control around the Secure Element. In the same vein, the value MCX brings to merchants – is the collective negotiating power of over 30 national merchants. But is it a new consumer brand, or is it a platform focused on routing the transaction over the least cost routing option. If its the latter, then it has a strong parallel in Paypal. And as we may see Paypal pop-up as legal tender in many a retailer’s mobile apps and checkout aisles going forward, MCX is likely to succeed by emulating that retailer aligned strategy than follow a brand of its own. Further, If MCX wants customers to pay using less costly means – whether they be private label, prepaid or ACH – then it and its partners must do everything they can to shift the customer focus away from preferred payment methods and focus on the customer experience and resulting value around loyalty. MCX must build its value proposition elsewhere, and make their preferred payment methods the bridge to get the customer there. Another example where the retailer focused too much on the payment, and less so on the customer experience is the Safeway Fast Forward program. The value proposition is clear for the customer – Pay using your Safeway Fast Forward card number and a self assigned PIN for simpler checkout. However to set up your account, the customer must provide a State issued ID (Drivers License) and on top of it – his Social Security Number(Safeway Fast Forward Requirements Here). What customer would, for the incremental convenience of paying via his Fast Forward Card and PIN, be willing to entrust Safeway with his Social Security Number? Clearly Safeway’s Risk team had a say in this and instead of coming up with better ways to answer questions around Risk and Fraud, they introduced a non-starter, which killed any opportunity for meaningful adoption. MCX & adoption So where does that leave MCX? Why will I use it? How will it address questions around adoption? It’s a given that it will have to answer the same questions around fraud and authentication during customer on-boarding or at a transactional level. Further, its not enough these days to simply answer questions pertaining to the customer. Further, one must address questions relating to the integrity and reputation of the device the customer use – whether that be a mobile device or a Laptop PC. But beyond fraud and auth, there are difficult questions around what would compel a techno-luddite who has historically paid using a credit instrument to opt for an ACH driven(i am guessing) MCX payment scheme. Well, for one: MCX and its retail partners can control the purchasing power parity of MCX credits. If they so wish, and after aggregating customer profiles across retailers, MCX determines that the Addams family spends a collective $400 on average per month between all the MCX retailers. MCX could propose that if instead, the Addams family were to commit to buy $450 in MCX credits each month, they could increase their purchasing power an additional $45 credits that could be used on specific retail categories (or flat out across all merchandise)? Would Morticia be interested? If she did, what does that mean to MCX? It eliminated having to pay interchange on approx $500, and further it enabled its partners to capture an incremental spend of 10% that did not exist before. Only merchants will be able to pull this off – by leveraging past trends, close relationships with CPG manufacturers and giving Morticia new reasons to spend in the manner they want her to. But then again, where does MCX stop in providing a level playing field for its partners, and step back – so that merchants can start to compete for their customers and their spend? And finally, can it survive the natural conflicts that will arise, and limit its scope to areas that all can agree – for long enough for it to take root? Should MCX become the next Isis or the next Paypal? Which makes most sense? What do you think? Please leave your opinions below... (This blog post is an adaptation of its original post found - http://www.droplabs.co/?p=662)