Digital Technology

James W. Paulsen, Chief Investment Strategist for Wells Capital Management, kicked off the second day of Experian’s Vision 2016, sharing his perspective on the state of the economy and what the future holds for consumers and businesses alike. Paulsen joked this has been “the most successful, disappointing recovery we’ve ever had.” While media and lenders project fear for a coming recession, Paulsen stated it is important to note we are in the 8th year of recovery in the U.S., the third longest in U.S. history, with all signs pointing to this recovery extending for years to come. Based on his indicators – leverage, restored household strength, housing, capital spending and better global growth – there is still capacity to grow. He places recession risk at 20 to 25 percent – and only quotes those numbers due the length of the recovery thus far. “What is the fascination with crisis policies when there is no crisis,” asks Paulsen. “I think we have a good chance of being in the longest recovery in U.S. history.” Other noteworthy topics of the day: Fraud prevention Fraud prevention continues to be a hot topic at this year’s conference. Whether it’s looking at current fraud challenges, such as call-center fraud, or looking to future-proof an organization’s fraud prevention techniques, the need for flexible and innovative strategies is clear. With fraudsters being quick, and regularly ahead of the technology fighting them, the need to easily implement new tools is fundamental for you to protect your businesses and customers. More on Regulatory The Military Lending Act has been enhanced over the past year to strengthen protections for military consumers, and lenders must be ready to meet updated regulations by fall 2016. With 1.46 million active personnel in the U.S., all lenders are working to update processes and documentation associated with how they serve this audience. Alternative Data What is it? How can it be used? And most importantly, can this data predict a consumer’s credit worthiness? Experian is an advocate for getting more entities to report different types of credit data including utility payments, mobile phone data, rental payments and cable payments. Additionally, alternative data can be sourced from prepaid data, liquid assets, full file public records, DDA data, bill payment, check cashing, education data, payroll data and subscription data. Collectively, lenders desire to assess someone’s stability, ability to pay and willingness to repay. If alternative data can answer those questions, it should be considered in order to score more of the U.S. population. Financial Health The Center for Financial Services Innovation revealed insights into the state of American’s financial health. According to a study they conducted, 57 percent of Americans are not financially healthy, which equates to about 138 million people. As they continue to place more metrics around defining financial health, the center has landed on four components: how people plan, spend, save and borrow. And if you think income is a primary factor, think again. One-third of Americans making more than $60k a year are not healthy, while one-third making less than $60k a year are healthy. --- Final Vision 2016 breakouts, as well as a keynote from entertainer Jay Leno, will be delivered on Wednesday.

It’s impossible to capture all of the insights and learnings of 36 breakout sessions and several keynote addresses in one post, but let’s summarize a few of the highlights from the first day of Vision 2016. 1. Who better to speak about the state of our country, specifically some of the threats we are facing than Leon Panetta, former Secretary of Defense and Director of the CIA. While we are at a critical crossroads in the United States, there is room for optimism and his hope that we can be an America in Renaissance. 2. Alex Lintner, Experian President of Consumer Information Services, conveyed how the consumer world has evolved, in large part due to technology: 67 percent of consumers made purchases across multiple channels in the last six months. More than 88M U.S. consumers use their smartphone to do some form of banking. 68 percent of Millennials believe within five years the way we access money will be totally different. 3. Peter Renton of Lend Academy spoke on the future of Online Marketplace Lending, revealing: Banks are recognizing that this industry provides them with a great opportunity and many are partnering with Online Marketplace Lenders to enter the space. Millennials are not the largest consumers in this space today, but they will be in the future. Sustained growth will be key for this industry. The largest platforms have everything they need in place to endure – even through an economic downturn.In other words, Online Marketplace Lenders are here to stay. 4. Tom King, Experian’s Chief Information Security Officer, addressed the crowds on how the world of information security is growing increasingly complex. There are 1.9 million records compromised every day, and sadly that number is expected to rise. What can businesses do? “We need to make it easier to make the bad guys go somewhere else,” says King. 5. Look at how the housing market has changed from just a few years ago: Inventory continues to be extraordinarily lean. Why? New home building continues to run at recession levels. And, 8.5 percent of homeowners are still underwater on their mortgage, preventing them from placing it on the market. In the world of single-family home originations, 2016 projections show that there will be more purchases, less refinancing and less volume. We may see further growth in HELOC’s. With a dwindling number of mortgages benefiting from refinancing, and with rising interest rates, a HELOC may potentially be the cheapest and easiest way to tap equity. 6. As organizations balance business needs with increasing fraud threats, the important thing to remember is that the customer experience will trump everything else. Top fraud threats in 2015 included: Card Not Present (CNP) First Party Fraud/Synthetic ID Application Fraud Mobile Payment/Deposit Fraud Cross-Channel FraudSo what do the experts believe is essential to fraud prevention in the future? Big Data with smart analytics. 7. The need for Identity Relationship Management can be seen by the dichotomy of “99 percent of companies think having a clear picture of their customers is important for their business; yet only 24 percent actually think they achieve this ideal.” Connecting identities throughout the customer lifecycle is critical to bridging this gap. 8. New technologies continue to bring new challenges to fraud prevention. We’ve seen that post-EMV fraud is moving “upstream” as fraudsters: Apply for new credit cards using stolen ID’s. Provision stolen cards into mobile wallet. Gain access to accounts to make purchases.Then, fraudsters are open to use these new cards everywhere. 9. Several speakers addressed the ever-changing regulatory environment. The Telephone Consumer Protection Act (TCPA) litigation is up 30 percent since the last year. Regulators are increasingly taking notice of Online Marketplace Lenders. It’s critical to consider regulatory requirements when building risk models and implementing business policies. 10. Hispanics and Millennials are a force to be reckoned with, so pay attention: Millennials will be 81 million strong by 2036, and Hispanics are projected to be 133 million strong by 2050. Significant factors for home purchase likelihood for both groups include VantageScore® credit score, age, student debt, credit card debt, auto loans, income, marital status and housing prices. More great insights from Vision coming your way tomorrow!

This article first appeared in Baseline Magazine Since it is possible for cyber-criminals to create a synthetic person, businesses must be able to differentiate between synthetic and true-party identities. Children often make up imaginary friends and have a way of making them come to life. They may come over to play, go on vacation with you and have sleepover parties. As a parent, you know they don’t really exist, but you play along anyway. Think of synthetic identities like imaginary friends. Unfortunately, some criminals create imaginary identities for nefarious reasons, so the innocence associated with imaginary friends is quickly lost. Fraudsters combine and manipulate real consumer data with fictitious demographic information to create a “new” or “synthetic” individual. Once the synthetic person is “born,” fraudsters create a financial life and social history that mirrors true-party behaviors. The similarities in financial activities make it difficult to detect good from bad and real from synthetic. There really is no difference in the world of automated transaction processing between you and a synthetic identity. Often the synthetic “person” is viewed as a thin or shallow file consumer— perhaps a millennial. I have a hard time remembering all of my own passwords, so how do organized “synthetic schemes” keep all the information usable and together across hundreds of accounts? Our data scientists have found that information is often shared from identity to identity and account to account. For instance, perhaps synthetic criminals are using the same or similar passwords or email addresses across products and accounts in your portfolio. Or, perhaps physical address and phone records have cross-functional similarities. The algorithms and sciences are much more complex, but this simplifies how we are able to link data, analytics, strategies and scores. Identifying the Business Impact of Synthetic-Identity Fraud Most industry professionals look at synthetic-identity fraud as a relatively new fraud threat. The real risk runs much deeper in an organization than just operational expense and fraud loss dollars. Does your fraud strategy include looking at all types of risk, compliance reporting, and how processes affect the customer experience? To identify the overall impact synthetic identities can have on your institution, you should start asking: Are you truly complying with "Know Your Customer" (KYC) regulations when a synthetic account exists in your active portfolio? Does your written "Customer Identification Program" (CIP) include or exclude synthetic identities? Should you be reporting this suspicious activity to the compliance officer (or department) and submitting a suspicious activity report (SAR)? Should you charge off synthetic accounts as credit or fraud losses? Which department should be the owner of suspected synthetic accounts: Credit Risk, Collections or Fraud? Do you have run any anti-money laundering (AML) risk when participating in money movements and transfers? Depending on your answers to the above questions, you may be incurring potential risks in the policies and procedures of synthetic identity treatment, operational readiness and training practices. Since it is possible to create a synthetic person, businesses must be able to differentiate between synthetic and true-party identities, just as parents need to differentiate between their child's real and imaginary friends.

A recent Experian study reveals that tax filing, document collection and refund processing are done online more often, yet only 6% of consumers file taxes on a computer with up-to-date antivirus software. 79% filed their most recent tax return online, up from 73% in 2011 18% scan and save their tax documents electronically, up from 6% in 2011 More than 75% of respondents have used EFT for tax refunds As electronic filing continues to grow, identity theft is likely to increase. While consumers should take steps to protect themselves, businesses also need to employ identity theft protection solutions to safeguard consumer information. >> Identify and prevent fraud

Device emulators — wolves in sheep’s clothing Despite all the fraud prevention systems and resources in the public and private sectors, online fraud continues to grow at an alarming rate, offering a low-risk, high-reward proposition for fraudsters. Unfortunately, the Web houses a number of easily accessible tools that criminals can use to perpetrate fraud and avoid detection. The device emulator is one of these tools. Simply put, a device emulator is one device that pretends to be another. What began as innovative technology to enable easy site testing for Web developers quickly evolved into a universally available tool that attackers can exploit to wreak havoc across all industry verticals. While it’s not new technology, there has been a significant increase in its use by criminals to deceive simple device identification and automated risk-management solutions to carry out fraudulent activities. Suspected device emulation (or spoofing) traffic historically has been difficult to identify because fraud solutions rely heavily on reputation databases or negative lists. Detecting and defeating these criminals in sheep’s clothing is possible, however. Leveraging Experian’s collective fraud intelligence and data modeling expertise, our fraud research team has isolated several device attributes that can identify the presence of an emulator being used to submit multiple transactions. Thanks to these latest FraudNet rule sets, financial institutions, ecommerce merchants, airlines, insurers and government entities alike now can uncloak and protect against many of these cybercriminals. Unfortunately, device emulators are just one of many tools available to criminals on the Dark Web. Join me at Vision 2016, where U.S. Secret Service and I will share more tales from the Dark Web. We will explore the scale of the global cybercrime problem, walk through the anatomy of a typical hack, explain how hackers exploit browser plug-ins, and describe how enhanced device intelligence and visibility across all channels can stop fraudsters in their tracks. Listen to Mike Gross as he shares a short overview of his Vision 2016 breakout session in this short video. Don’t miss this innovative Vision 2016 session! See you there.

Identity management traditionally has been made up of creating rigid verification processes that are applied to any access scenario. But the market is evolving and requiring an enhanced Identity Relationship Management strategy and framework. Simply knowing who a person is at one point in time is not enough. The need exists to identify risks associated with the entire identity profile, including devices, and the context in which consumers interact with businesses, as well as to manage those risks throughout the consumer journey. The reasoning for this evolution in identity management is threefold: size and scope, flexible credentialing and adaptable verification. First, deploying a heavy identity and credentialing process across all access scenarios is unnecessarily costly for an organization. While stringent verification is necessary to protect highly sensitive information, it may not be cost-effective to protect less-valuable data with the same means. A user shouldn’t have to go through an extensive and, in some cases, invasive form of identity verification just to access basic information. Second, high-friction verification processes can impede users from accessing services. Consumers do not want to consistently answer multiple, intrusive questions in order to access basic information. Similarly, asking for personal information that already may have been compromised elsewhere limits the effectiveness of the process and the perceived strength in the protection. Finally, an inflexible verification process for all users will detract from a successful customer relationship. It is imperative to evolve your security interactions as confidence and routines are built. Otherwise, you risk severing trust and making your organization appear detached from consumer needs and preferences. This can be used across all types of organizations — from government agencies and online retailers to financial institutions. Identity Relationship Management has three unique functions delivered across the Customer Life Cycle: Identity proofing Authentication Identity management Join me at Vision 2016 for a deeper analysis of Identity Relationship Management and how clients can benefit from these new capabilities to manage risk throughout the Customer Life Cycle. I look forward to seeing you there!
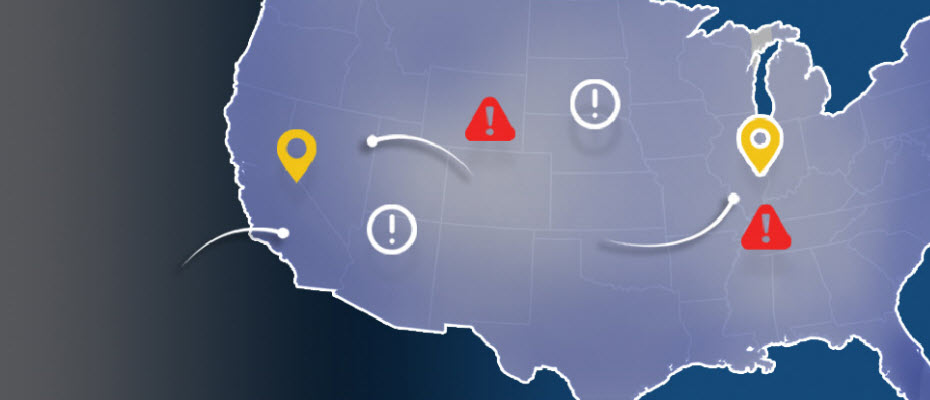
Top states for billing and shipping e-commerce fraud With more than 13 million fraud victims in 2015, assessing where fraud occurs is an important layer of verification for e-commerce. Experian® analyzed millions of e-commerce transactions from 2015 to identify fraud attack rates across the United States. With the switch to chip-enabled credit card transactions and possible growth of card-not-present fraud, online businesses should utilize advanced fraud solutions to monitor their riskiest locations and prevent losses. >> View the Experian map to see 2015 e-commerce attack rates for all states
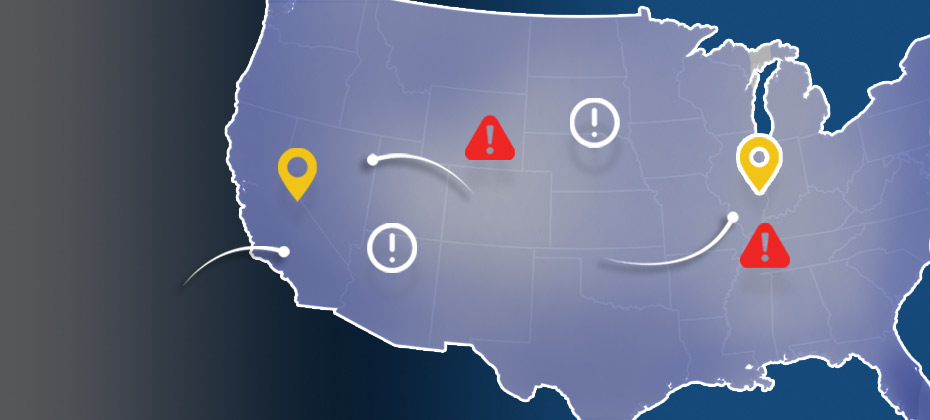
2015 data shows where billing and shipping e-commerce fraud attacks occur in the United States Experian e-commerce fraud attacks and rankings now available Does knowing where fraud takes place matter? With more than 13 million fraud victims in 2015,[1] assessing where fraud occurs is an important layer of verification when performing real-time risk assessments for e-commerce. Experian® analyzed millions of e-commerce transactions from 2015 data to identify fraud-attack rates across the United States for both shipping and billing locations. View the Experian map to see 2015 e-commerce attack rates for all states and download the top 100 ZIP CodeTMrankings. “Fraud follows the path of least resistance. With more shipping and billing options available to create a better customer experience, criminals attempt to exploit any added convenience,” said Adam Fingersh, Experian general manager and senior vice president of Fraud & Identity Solutions. “E-commerce fraud is not confined to larger cities since fraudsters can ship items anywhere. With the switch to chip enabled credit card transactions, and possible growth of card-not-present fraud, our fraud solutions help online businesses monitor their riskiest locations to prevent losses both in dollars and reputation in the near term.” For ease of interpretation, billing states are associated with fraud victims (the address of the purchaser) and shipping states are associated with fraudsters (the address where purchased goods are sent). According to the 2015 e-commerce attack rate data: Florida is the overall riskiest state for billing fraud, followed by Delaware; Washington, D.C.; Oregon and California. Delaware is the overall riskiest state for shipping fraud, followed by Oregon, Florida, California and Nevada. Eudora, Kan., has the overall riskiest billing ZIP Code (66025). The next two riskiest ZIPTM codes are located in Miami, Fla. (33178) and Boston, Mass. (02210). South El Monte, Calif., has the overall riskiest shipping ZIP Code (91733). The next four riskiest shipping ZIP codes are all located in Miami. Overall, five of the top 10 riskiest shipping ZIP codes are located in Miami. Defiance, Ohio, has the least risky shipping ZIP Code (43512). The majority of U.S. states are at or below the average attack rate threshold for both shipping and billing fraud, with only seven states — Florida, Oregon, Delaware, California, New York, Georgia and Nevada — and Puerto Rico ranking higher than average. This indicates that attackers are targeting consumers equally in the higher-risk states while leveraging addresses from both higher- and lower-risk states to ship and receive fraudulent merchandise. Many of the higher-risk states are located near a large port-of-entry city, including Miami; Portland, Ore.; and Washington, D.C., perhaps allowing criminals to move stolen goods more effectively. All three cities are ranked among the riskiest cities for both measures of fraud attacks. Neighboring proximity to higher-risk states does not appear to correlate to any additional risk — Pennsylvania and Rhode Island are ranked as two of the lower-risk states for both shipping and billing fraud. Other lower-risk states include Wyoming, South Dakota and West Virginia. Experian analyzed millions of e-commerce transactions to calculate the e-commerce attack rates using “bad transactions” in relation to the total number of transactions for the 2015 calendar year. View the Experian map to see 2015 e-commerce attack rates for all states and download the top 100 ZIP Code rankings. [1]According to the February 2016 Javelin study 2016 Identity Fraud: Fraud Hits an Inflection Point.

A recent Experian survey shows a growing concern over identity theft and tax fraud. 42% of consumers are concerned that someone could access their personal data through their tax return, compared with 35% in 2014 and 38% in 2015 28% of consumers have been a victim or know someone who has been a victim of tax fraud Tax season is a busy time of year for identity thieves. While consumers should take steps to protect themselves, businesses also need to employ ID theft protection solutions in order to safeguard consumer information. >> Identify and prevent multiple types of fraud

What is blockchain? Blockchain is beginning to get a lot of attention, so I thought it might be time to figure out what it is and what it means. Basically, a blockchain is a permissionless, distributed database that maintains a growing list of records (transactions) in a linear, chronological (and time-stamped) ledger. At a high level, this is how it works. Each computer connected to the network gets a copy of the entire blockchain and performs the task of validating and relaying transactions for the whole chain. The batches of valid transactions added to the record are called “blocks.” A block is the “current” part of a blockchain that records some or all of the recent transactions and once completed goes into the blockchain as a permanent database. Each time a block gets completed, a new block is created, with every block containing a hash of the previous block. There are countless numbers of blocks in the blockchain. To use a conventional banking analogy, the blocks would be a full history of every banking transaction for every person, and the blockchain would be a complete banking history. The entire blockchain is sent to everyone who has access, and every user validates the information in the block. It’s like if Tom, Bob and Harry were standing on the street corner and saw a cyclist hit by a car. Individually, all three men will be asked if the cyclist was struck by the car, and all three will respond “yes.” The cyclist being hit by the car becomes part of the blockchain, and that fact cannot be altered. Blockchain generally is used in the context of bitcoin, where similar uses of the structure are called altchains. Why should I care or, at the very least, pay attention to this movement? Because the idea of it is inching toward the tipping point of mainstream. I recently read an article that identified some blockchain trends that could shape the industry in coming months. The ones I found most interesting were: Blockchain apps will be released Interest in use cases outside payments will pick up Consortia will prove to be important Venture capital money will flow to blockchain start-ups While it’s true that much of the hype around blockchain is coming from people with a vested interest, it is beginning to generate more generalized market buzz as its proponents emphasize how it can reduce risk, improve efficiency and ultimately provide better customer service. Let’s face it, the ability to maintain secure, fast and accurate calculations could revolutionize the banking and investment industries, as well as ecommerce. In fact, 11 major banks recently completed a private blockchain test, exchanging multiple tokens among offices in North America, Europe and Asia over five days. (You can read The Wall Street Journal article here.) As more transactions and data are stored in blockchain or altchain, greater possibilities open up. It’s these possibilities that have several tech companies, like IBM, as well as financial institutions creating what has become known as an open ledger initiative to use the blockchain model in the development of new technologies that will enable a wider array of services. There is no doubt that the concept is intriguing — so much so that even the SEC has approved a plan to issue stock via blockchain. (You can read the Wired article here.) The potential is enough to make many folks giddy. The idea that risk could become a thing of the past because of the blockchain’s immutable historical record — wow. It’s good to be aware and keep an eye on the open ledger initiative, but let’s not forget history, which has taught us that (in the wise words of Craig Newmark), “Crooks are early adopters.” Since blockchain’s original and primary usage has been with bitcoin, I don’t think it is unfair to say that there will be some perceptions to overcome — like the association of bitcoin to activities on the Dark Web such as money laundering, drug-related transactions and funding illegal activities. Until we start to see the application across mainstream use cases, we won’t know how secure blockchain is or how open business and consumers will be to embracing it. In the meantime, remind me again, how long has it taken to get to a point of practical application and more widespread use of biometrics? To learn more, click here to read the original article.

According to a recent Experian Marketing Services study, 36% of companies interact with customers in five or more channels.

Ensure you’re protecting consumer data privacy Data Privacy Day is a good reminder for consumers to take steps to protect their privacy online — and an ideal time for organizations to ensure that they are remaining vigilant in their fight against fraud. According to a new study from Experian Consumer Services, 93 percent of survey respondents feel identity theft is a growing problem, while 91 percent believe that people should be more concerned about the issue. Online activities that generate the most concern include making an online purchase (73 percent), using public Wi-Fi (69 percent) and accessing online accounts (69 percent). Consumers are vigilant while online Most respondents are concerned they will fall victim to identity theft in the future (71 percent), resulting in a generally proactive approach to protecting personal information. In fact, almost 50 percent of respondents say they are taking more precautions compared with last year. Ninety-one percent take steps to secure physical information, such as shredding documents, while also securing digital information (using passwords and antivirus software). Many consumers also make sure to check their credit report (33 percent) and bank account statements (76 percent) at least once per month. There’s still room for consumers to be safer Though many consumers are practicing good security habits, some aren’t: More than 50 percent do not check to see if a Website is secure Fifty percent do not have all their Web-enabled devices password-protected because it is a hassle to enter a password (30 percent) or they do not feel it is necessary (25 percent) Fifty-five percent do not close the Web browser when they are finished using an online account Additionally, 15 percent keep a written record of passwords and PINs in their purse or wallet or on a mobile device or computer Businesses need to be responsible when it comes data privacy Customer-facing businesses must continue efforts to educate consumers about their role in breach and fraud prevention. They also need to be responsible and apply comprehensive, data-driven intelligence that helps thwart both breaches and the malicious use of breached information and protect all parties’ interests. Nearly 70 percent of those polled in a 2015 Experian–Ponemon Institute study said that the increased visibility and media reporting of breaches, including payment-related incidents, have caused their organizations to step up data security efforts. Experian Fraud & ID is uniquely positioned to provide true customer intelligence by combining identity authentication with device assessment and monitoring from a single integrated provider. This combination provides the only true holistic view of the customer and allows organizations to both know and recognize customers and to provide them with the best possible experience. By associating the identities and the devices used to access services, the true identity can be seen across the customer journey. This unique and integrated view of identity and device delivers proven superior performance in authentication, fraud risk segmentation and decisioning. For more insights into how businesses are responding to breach activities, download our recent white paper, Data confidence realized: Leveraging customer intelligence in the age of mass data compromise. For more findings from the study, view the results here.

Attract and retain high-value demand deposit accounts The excitement of the new year has ended, and now the big question remains: What will 2016 hold for our market and the economy? So far, we’ve seen this election year bring a volatile financial market: The Federal Reserve increased short-term interest rates by 25 basis in December, and there is uncertainty if and when future increases will come China’s gross domestic product is forecasted at 6.5 percent, the lowest in a quarter century The Dow Jones industrial average is down 10 percent to start the year, signaling a lot of uncertainty for banks and consumers It’s hard to find answers in a shifting financial landscape with a long list of mixed signals. The average consumer is looking on and wondering if we face another Great Recession or if the current economy is spiking a fever just before it is completely cured. The reality, for those of us in the banking industry, is that the modest economic recovery is likely to continue as part of a new normal pattern. In 2016, banks that remain competitive in a more digital world will be those that have frictionless products and processes to attract and retain high-value, highly sought-after consumer deposits and loans. Banks should expect the competition for deposits to intensify, and they will need to ensure that new deposit customers are on boarded effectively and cross-sold loan products quickly to reduce first-year attrition. Cross-selling at the point of origination for the demand deposit account (DDA) customers is the best way to ensure that new customers keep the institution as their primary bank. Financial institutions can exceed consumer expectations and ensure a competitive business model by leveraging modernized technology capabilities fully in combination with making relevant decisions to deliver consumer-friendly experiences. First-year DDA attrition rates will demonstrate how the consumer’s expectations were met and if the new bank got the account-opening process right or wrong. Experian® suggests three capabilities clients should consider: A deposits technology platform that offers frictionless change to data, origination strategies and instant cross-sell to loan products that yield sticky customers Strategies that comply with current and evolving regulatory demands, such as those being sought by the Consumer Financial Protection Bureau (CFPB) Business planning to identify execution gaps and a road map to ensure that gaps are addressed, confirming continued competitive ability to attract high-value deposit and loan customers DDA-account opening effectiveness can be achieved by using a consumer’s life stage, affordability considerations, unique risk profile and financial needs to on board optimally and grow those high-value consumers effectively and efficiently. Financial institutions that are nimble and fast adopters of these critical capabilities will reduce operating expenses for their organizations, grow sustainable revenue from new prospects and customers, and delight those new customers along the way. This is a win-win for banks and consumers. Join me next week as we discuss best practices across the entire demand deposit account life cycle.

Payments and the Internet of things has been colliding for a while now – and it surfaced again recently with Mastercard announcing that it is working with an array of partners including Capital One to launch payments in connected devices. The thinking here seems to be that payments is a function in the Marlow’s pyramid of needs for any new consumer device. I am conflicted on this point – not that I don’t believe the Internet of Things isn’t important, but that we may be overthinking in how payments is important to be shoved inside everything that has a radio baked in. And not everything will have a radio in the future, and the role of a smartphone as the center of the connected device commerce universe isn’t going away. It is important to keep perspective here – as this announcement is less about coat sleeves hiding NFC chips with tokenized credit cards – rather it’s the commerce enablement of devices that we may carry on our person so that they can be armed for payment. Though I may disagree on whether a coat sleeve or jewelry are essential end-points in commerce, a platform of capabilities to challenge, authenticate and verify, and ultimately trust and provision a tokenized representation of something, whether its a card or a fragment of a consumer's identity, to a device that itself represents a collection of radios and sensors is very exciting. It is exciting because as device counts and assortments grow, they each have their own residual identity as a combination of things and behaviors that are either deterministic or probabilistic. The biggest shift we will see is that the collective device identities can be a far better and complete representation of customer identity that the latter will be replaced by the former. Name-centric identities will give away to algorithmically arrived ones. As Dan Geer puts it, no longer will I need to announce that I am Cherian, but my collection of devices will indeed do so on my behalf, perhaps in consultation with each other. More over, none of these devices need to replicate my identity in order to be trusted and tethered, either. Coming back to Payments, today my Fitbit’s claim to make a successful payment is validated way before the transaction, when I authorized provisioning by authenticating through a bank app or wallet. What would be interesting is when the reverse becomes true – when these class of devices that I own can together or separately vouch for my identity. We may forget usernames and passwords, fingerprints may prove to be irrevocable and rigid, but we will always be surrounded by a fog of devices that each carry a cryptographically unique and verifiable signature. And it will be up to the smartphone, its ecosystem and the devices that operate in its periphery to individually negotiate and establish trust among each of them. So this is why I believe the MasterCard effort in tokenizing devices is important when you view it in conjunction with the recent launch of SwiftID from CapitalOne. Payments getting shoved in to everyday things like wearables, disguises the more important effort of becoming a beachhead in establishing trust between devices, by using tokenization as the method of delivery. As you may have gathered by now, I am less excited of pushing cards in to devices (least of all – cars!) and more about how a trusted framework to carve out a tamper proof and secure cache within an untrusted device, along with the process to securely provision a token or a signed hash representing something of value, can serve as the foundation for future device – and by extension – user identity. On a side note, here’s a bit about pushing cards in to cars, and mistaking them for connected cars. To me there are only two connected car classes today. One is Tesla where each car on the road is part of the whole, each learning separately and together as they examine, encounter and learn the world around them to maneuver safely. The other is a button in an app that I hit to have a car magically appear in front of me. Other than Tesla and Uber, there are no other commercial instances of a connected car that appeals (Google has no cars you can buy, yet).

Leveraging customer intelligence in the age of mass data compromise Hardly a week goes by without the media reporting a large-scale hack of sensitive personal or account information. Increasingly, the public seems resigned to believe that such compromises are the new normal, producing a kind of breach fatigue that may be lowering the expectations consumers have for identity and online security. Still, businesses must be vigilant and continue to apply comprehensive, data-driven intelligence that helps to thwart both breaches and the malicious use of breached information and to protect all parties’ interests. We recently released a new white paper, Data confidence realized: Leveraging customer intelligence in the age of mass data compromise, to help businesses understand how data and technology are needed to strengthen fraud risk strategies through comprehensive customer intelligence. At its core, reliable customer intelligence is based on high-quality contextual identity and device attributes and other authentication performance data. Customer intelligence provides a holistic, bound-together view of devices and identities that equips companies and agencies with the tools to balance cost and risk without increasing transactional friction and affecting the customer experience. In the age of mass data compromise, however, obtaining dependable information continues to challenge many companies, usually because consumer-provided identities aren’t always unique enough to produce fully confident decisioning. For more information, and to get a better sense of what steps you need to take now, download the full white paper.