Financial Services

What the EMV Shift means for you I recently facilitated a Webinar looking at myths and truths in the market regarding the EMV liability shift and what it means for both merchants and issuers. I found it to be a very beneficial discussion and wanted to take some time to share some highlights from our panel with all of you. Of course, if you prefer to hear it firsthand, you can download the archive recording here. Myth #1: Oct. 1 will change everything Similar to the hype we heard prior to Y2K, Oct. 1, 2015, came and went without too much fanfare. The date was only the first step in our long and gradual path to EMV adoption. This complex, fragmented U.S. migration includes: More than 1 billion payment cards More than 12 million POS terminals Four credit card networks Eighteen debit networks More than 12,000 financial institutions Unlike the shift in the United Kingdom, the U.S. migration does not have government backing and support. This causes additional fragmentation and complexity that we, as the payments industry, are forced to navigate ourselves. Aite Group predicts that by the end of 2015, 70 percent of U.S. credit cards will have EMV capabilities and 40 percent of debit cards will be upgraded. So while Oct. 1 may not have changed everything, it was the start of a long and gradual migration. Myth #2: Subscription revenues will plummet due to reissuances According to Aite, EMV reissuance is less impactful to merchant revenues than database breaches, since many EMV cards are being reissued with the same pan. The impact of EMV on reoccurring transactions is exaggerated in the market, especially when you look at the Update Issuer provided by the transaction networks. There still will be an impact on merchants, coming right at the start of the holiday shopping season. The need for consumer education will fall primarily on merchants, given longer lines at checkout and unfamiliar processes for consumers. Merchants should be prepared for charge-back amounts on their statements, which they aren’t used to seeing. Lastly, with a disparate credit and debit user experience, training is needed not just for consumers, but also for frontline cashiers. We do expect to see some merchants decide to wait until after the first of the year to avoid impacting the customer experience during the critical holiday shopping season, preferring to absorb the fraud in the interest of maximizing consumer throughout. Myth #3: Card fraud will decline dramatically We can look to countries that already have migrated to see that card fraud will not, as a whole, decline dramatically. While EMV is very effective at bringing down counterfeit card fraud, organized crime rings will not sit idly by while their $3 billion business disappears. With the Canadian shift, we saw a decrease in counterfeit card loss but a substantial increase in Card Not Present (CNP) fraud. In Canada and Australia, we also saw a dramatic, threefold increase in fraudulent applications. When criminals can no longer get counterfeit cards, they use synthetic and stolen identities to gain access to new, legitimate cards. In the United States, we should plan for increased account-takeover attacks, i.e., criminals using compromised credentials for fraudulent CNP purchases. For merchants that don’t require CVV2, compromised data from recent breaches can be used easily in an online environment. According to Aite, issuers already are reporting an increase in CNP fraud. Fraudsters did not wait until the Oct. 1 shift to adjust their practices. Myth #4: All liability moves to the issuer EMV won’t help online merchants at all. Fraud will shift to the CNP channel, and merchants will be completely responsible for the fraud that occurs there. We put together a matrix to illustrate where actual liability shifts and where it does not. Payments liability matrix Note: Because of the cost and complexity of replacing POS machines, gas stations are not liable until October 2017. For more information, or if you’d like to hear the full discussion, click here to view the archive recording, which includes a great panel question-and-answer session.

While walking through a toy store in search of the perfect gift for a nephew, I noticed the board game Risk, which touts itself as “The Game of Global Domination.” For those who are unaware, the game usually is won by players who focus on four key themes: Strategy — Before you begin the game, you need a strategy to attack new territories while defending your own Attack — While you have the option to sit back and defend your territory, it’s better to attack a weakened opponent Fortify — When you are finished attacking, it’s often best to fortify your position Alliances — While not an official part of the game, creating partnerships is necessary in order to win These themes also are relevant to the world of real-life fraud risk prevention. The difference is that the stakes are real and much higher. Let’s look at how these themes play out in real-life fraud risk prevention: Strategy — Like in the game, you need a strategy for fraud risk detection and prevention. That strategy must be flexible and adaptable since fraudsters (your enemies) also continuously adapt to changing environments, usually at a much quicker, less bureaucratic pace. For example, your competitors (other countries) may improve their defenses, so fraudsters will mount a more focused attack on you. Fraudsters also may build alliances to attack you from different vectors or channels, resulting in a more sophisticated, comprehensive strike. Attack — As the game begins, all players have access to all competitors (countries). This means that fraudsters might have the upper hand in a certain area of the business. You can sit back and try to defend the territory you already “own,” where fraudsters have no traction, but it’s best to be aggressive and attack fraudsters by expanding your coverage across all channels. For example, you might have plenty of controls in place to manage your Web orders (occupied territory), but your call center operations (opponents’ territory) aren’t protected, i.e., the fraudsters “own” this space. You need to attack that channel to drive fraudsters out. Fortify — In the game, you can fortify your position after a successful move — that is, move more troops to your newly conquered territories. In real life, you always have the option to fortify your position, and you should constantly look for ways to improve your controls. You can’t afford to maintain on your current position, because fraudsters constantly are looking for weaknesses. Alliances — In business, we often are hesitant to share information with our competitors. Fraudsters use this to their advantage. Just as fraudsters act in a coordinated fashion, so must we. Use all available resources and partners to shore up your defenses Leverage the power of consortium data Learn new methods from traditional competitors Always team up with internal and external partners to defend your territory If you apply these themes, you will be positioned for global domination in the fight against fraud risk. You can read more about fraud-prevention strategies in our recent ebook, Protecting the Customer Experience. As a side note, I’m always ready for a game of Risk, so contact me if you’re interested. But be forewarned — I’m competitive.

What will the EMV shift really mean for consumers and businesses here in the U.S.? Businesses and consumers across the U.S. are still adjusting to their new EMV credit cards. The new credit cards are outfitted with computer chips in addition to the magnetic strips to help prevent point-of-sale (POS) fraud. The new system, called EMV (which stands for Europay, MasterCard and Visa), requires signatures for all transactions. EMV is a global standard for credit cards. In the wake of the rising flood of large-scale data breaches at major retailers – and higher rates of counterfeit credit card fraud – chip-and-signature, as it is also called, is designed to better authenticate credit card transactions. Chip-and-signature itself is not new. It has been protecting consumers and businesses in Europe for several years and now the U.S. is finally catching up. But what will the EMV system really mean for consumers and businesses here in the U.S.? There is the potential for businesses that sell both offline and online, to see an increase in fraud that takes place online called Card Not Present (CNP) fraud. Will credit card fraud ever really be wiped out? Can we all stop worrying that large-scale point-of-sale breaches will happen again? Will the EMV shift affect holiday shopping and should retailers be concerned? Join us as we explore these questions and more on an upcoming Webinar, Chipping Away at EMV Myths. Our panel of experts includes: David Britton, Vice President, Industry Solutions, Experian Julie Conroy, Research Director, Aite Group Mike Klumpp, Director of Fraud Prevention, Citibank Moderated by: Keir Breitenfeld, Vice President, Product Management, Experian

Commerce: A conversation between merchants and consumers Last week I joined Sherri Haymond of MasterCard and Bharathi Ramavarjula of Facebook on a panel moderated by Paul Moreton, for a CapitalOne summit on Payments. When asked what was more important for the future of commerce – Sherri spoke of how security and trust is key, and I talked about how messaging has intersected with payments, (and in Wechat’s case) now intersecting with lending – with Bharathi eloquently summing it up as – “Facebook sees Commerce as a conversation”. If Commerce is a conversation between a merchant and a consumer (however loosely defined those terms have now come to be), then it has become contorted and clustered around payments and point of sale. Till not too long ago, there also existed a high barrier for entry to become a merchant, to accept payments, to promote and sell online, and to find cheap capital for growth. All these things are different now – and unsurprisingly, little of this progress can be attributed to banks or other current payment stakeholders. For example: I didn’t know I could be a merchant till Square showed me how easy it is to accept credit cards, and setup a small business. I didn’t know that I could become a driver in my spare time – till Uber showed me how easy it is to become one. I didn’t know that I could become a landlord till AirBnB showed me how easy it is to find people to rent it to. I know I am oversimplifying. These three and others like them chose to use technology and smartphones to exponentially scale the size of existing two-sided markets as well as create new ones. When another billion people on the planet stand to be connected over the next five years – entirely via cheap smartphones – it is hard to view commerce as a zero sum opportunity. Being wired for commerce may come to mean something entirely different for those billion, and messaging apps and social networks will replace point of sale for discovery, acquisition and engagement. This is why I believe changes in payments today are largely incremental and localized to the developed world. The platform driven efforts – such as tokenization – do go beyond any specific modality (card, mobile, connected things) to further the notion and benefit of trust entirely within the network. But that is as far as it goes. Issuers and networks may have little role to play in discovery, consumer loyalty and now more so than ever – identity. Case in point: Through Relay, Stripe enables a retailer to push a button and start selling through new channels while taking comfort in that his pricing and inventory will remain real-time. Through Messenger and Shopping – Facebook will encapsulate product discovery, guide the intent to purchase, host the informed pre-purchase debate and even payment – flattening it and never letting it out of sight. It is no accident that each of the four horsemen of the Internet has heavily invested in voice assistants – (Apple/Siri, Google/Now, Facebook/M, Amazon/Echo, Microsoft/Cortana) – especially as we confront old habits in interaction design that are failing on mobile, to continue to shorten the distance between intent and action through things like 3D Touch, the Amazon Dash button, and intelligent agents. Everything that is interesting in commerce: product discovery, search, interface and interaction design are all being done – with the sole exception of Amazon – by an entity that is neither a retailer nor a bank. Conversational commerce does not end with payments being swallowed up by messaging apps. It is a pre-requisite, but hardly not even a way point in that journey. Originally posted on: Droplabs.co

Driver of success: Mitigate auto lending risk A culture of learning is a key driver of success. Does your risk culture continue to adapt? There are many issues within auto lending that are unique to other financial services ecosystems: the direct versus indirect relationship, insights of the asset influencing the risk insights, new versus used vehicle transactions influencing risk and terms, and more. However, there is one universal standard common to all financial services cultures — change.. Change is constant, and an institution’s marketing and risk organizations need to be constantly learning to stay abreast of dealer, consumer, competitor and regulatory issues. No one has said it better than Jack Welch: “An organization’s ability to learn, and translate that learning into action rapidly, is the ultimate competitive advantage.” This statement was quickly followed by a command: “Change before you have to.” So the challenge for the portfolio manager is to ensure there are the system features, data sources, management reporting structures, data access features, analytic skills, broad management team skill sets, and employee feedback and incentive plans to drive the organization to a constant state of renewal. The challenge for many smaller and midsize lenders is to determine what systems and skills need to be in-house and what tasks are better left for a third party to handle. For consumer-level data, vehicle history and valuation data, and fraud alert flags, it seems reasonable to leverage solutions from established third parties: credit reporting agencies. After that, the solutions to the many other needs may be more specific to the lender legacy skill set and other support relationships: Are there strong in-house data-management and analytic skills? There is a significant difference between management information and data analysis driving policy and portfolio performance forecasts. Does the internal team have both? Is the current operating platform(s) feature-rich and able to be managed and enhanced by internal resources within tight time frames? Is the management team broadly experienced and constantly updating best-practice insights? Is the in-house team frequently engaged with the regulatory community to stay abreast of new mandates and initiatives? There is a solution. Experian® offers the data, software, solutions, management information, analytic solutions and consulting services to tie everything together for a lender-specific best configuration. We look forward to hearing from you to discuss how we can help.

Key drivers to auto financial services are speed and precision. What model year is your decisioning system? In the auto world the twin engineering goals are performance and durability. Some memorable quotes have been offered about the results of all that complex engineering. And some not so complex observations. The world of racing has offered some best examples of the latter. Here’s a memorable one: “There’s no secret. You just press the accelerator to the floor and steer left. – Bill Vukovich When considering an effective auto financial services relationship one quickly comes to the conclusion that the 2 key drivers of an improved booking rate is the speed of the decision to the consumer/dealer and the precision of that decision – both the ‘yes/no’ and the ‘at what rate’. In the ‘good old days’ a lender relied upon his dealer relationship and a crew of experienced underwriters to quickly respond to a sales opportunities. Well, these days dealers will jump to the service provider that delivers the most happy customers. But, for all too many lenders some automated decisioning is leveraged but it is not uncommon to still see a significantly large ‘grey area’ of decisions that falls to the experienced underwriter. And that service model is a failure of speed and precision. You may make the decision to approve but your competition came in with a better price at the same time. His application got booked. Your decision and the cost incurred was left in the dust – bin. High on the list of solutions to this business issue is an improved use of available data and decisioning solutions. Too many lenders still underutilize available analytics and automated decisions to deliver an improved booking rate. Is your system last year’s model? Does your current underwriting system fully leverage available third party data to reduce delays due to fraud flags. Is your ability to pay component reliant upon a complex application or follow-up requests for additional information to the consumer? Does your management information reporting provide details to the incidence and disposition of all exception processes? Are you able to implement newer analytics and/or policy modifications in hours or days versus sitting in the IT queue for weeks or months? Can you modify policies to align with new dealer demographics and risk factors? The new model is in and Experian® is ready to help you give it a ride. Purchase auto credit data now.

As Big Data becomes the norm in the credit industry and others, the seemingly non-stop efforts to accumulate more and more data leads me to ask the question - when is Big Data too much data? The answer doesn’t lie in the quantity of data itself, but rather in the application of it – Big Data is too much data when you can’t use it to make better decisions. So what do I mean by a better decision? From any number of perspectives, the answer to that question will vary. From the viewpoint of a marketer, maybe that decision is about whether new data will result in better response rates through improved segmentation. From a lender perspective, that decision might be about whether a borrower will repay a loan or the right interest rate to charge the borrower. That is one the points of the hype around Big Data – it is helping companies and individuals in all sorts of situations make better decisions – but regardless of the application, it appears that the science of Big Data must not just be based on an assumption that more data will always lead to better decisions, but that more data can lead to better decisions – if it is also the “right data”. Then how does one know when another new data source is helping? It’s not obvious that additional data won’t help make a better decision. It takes an expert to understand not only the data employed, but ultimately the use of the data in the decision-making process. It takes expertise that is not found just anywhere. At Experian, one of our core capabilities is based on the ability to distinguish between data that is predictive and can help our clients make better decisions, and that which is noise and is not helpful to our clients. Our scores and models, whether they be used for prospecting new customers, measuring risk in offering new credit, or determining how to best collect on an outstanding receivable, are all designed to optimize the decision making process. Learn more about our big data capabilities

Protecting your customer The impact of fraud on the customer relationship Sadly fraudsters seem to always be one-step ahead of fraud-prevention strategies, causing organizations to play catch-up to the criminals. And as information security tightens and technologies evolve, so does the industrious nature of organized identity and online fraud. It should be no surprise then that fraud risk mitigation and management will continue to be an ongoing issue for organizations. But what continues to drive investment in identity management and online risk tools is the arms race across organizations to deliver superior customer experience and functionality. While the monetary cost of fraud losses can be high and rather detrimental, the impact of lost customers and overall reputational decline due to poor customer experiences can be higher. The key is finding the right balance between identifying and segmenting likely fraudulent customers across the vast majority of legitimate customers and transactions. I want to share a recent interactive eBook we launched which outlines the authentication and identity management balance with a focus on the consumer. We highlight current trends and what organizations should be thinking about and doing to protect their business, institution, or agency and customers. I hope you enjoy this look at the impact of fraud on the customer relationship.

Our clients are facing three primary issues when it comes to regulatory compliance: time resources knowledge Many are facing Matters Requiring Attention (MRA) and Matters Requiring Immediate Attention (MRIA) and don’t have the staff or the capacity to complete all of the work themselves within tight deadlines. They also want their limited resources to work on internal, proprietary initiatives to grow the business and maximize profit and return. These activities cannot be outsourced as easily as regulatory and compliance work, which is relatively easy to parse out and give to an external third party. Quite often, a level of independent oversight and effective challenge is also a requirement that can easily be solved through the use of an objective, external third party. A lot of the regulations are still relatively new, and there are still many issues and knowledge gaps our clients are facing. They have insight into their own organization only and quite often aren’t aware of or able to leverage industry best practice without the view of an external third party with broader industry knowledge and experience. In terms of best practice, it all really starts with the data, leading to the attributes used in models to create sound risk management strategies, manage capital adequacy, and ensure the safety and soundness of the overall U.S. and global financial system. The integrity of data reporting, dispute management and compliance with all applicable regulatory requirements need to be an enterprise-wide effort. In the area of attribute governance, there are three primary areas of focus: Attribution creation — definitions; logic, code and accuracy; and how to reduce implementation timelines. Monitoring and maintenance — looking for shifts in attributes and their potential impact and facilitating updates to attributes based upon changes in reporting and upgrades to newer versions of attributes as the credit environment changes, such as during the most recent mortgage crisis, where loan modification and associated attributes were created and took on increased importance. And last but definitely not least, documentation — We cannot say enough about the importance of documentation, especially to regulators. Documentation ensures accuracy and consistent application and must record all general conventions and limitations. For model risk management and governance, focus areas should follow the expanded Office of the Comptroller of the Currency (OCC) Guidance from Bulletin 2011-12. This guidance includes expanded requirements for model validations including not just standard back testing, but also benchmarking, effective challenge, sensitivity analysis and stress testing. It also expands the guidance beyond just validation to model development and usage, implementation, governance and controls. In response to these OCC expanded guidance requirements, one of our clients was seeking an industry expert to serve as an independent third party to 1) conduct industry best practice and benchmarking in areas of reject inference methodologies and 2) validate production models used for risk underwriting, line assignment, pricing and targeting. After a full review and assessment, we provided the client with a clear road map to improve the process to conduct reject inference through knowledge transfer and best practices. We established a best-in-class approach to annual model validations on a model inventory consisting of retail, small business and wealth segment portfolios. We also delivered expedited results that also identified alternative methods of validation that assess variability in point estimates, as well as comply with OCC requirements for precision, ranking and population measurement statistics. Through our work, the client was able to leverage Experian to establish a global approach to reject inference methodologies, to augment existing staffing and to offshore resources in a cost-effective manner. There are three primary areas of loss forecasting, stress testing and capital adequacy planning: International — Basel accord National — U.S. Dodd-Frank Act Stress Testing (DFAST), including Comprehensive Capital Analysis and Review (CCAR) supervisory review Internal — Allowance for Loan and Lease Losses requirements Although there are similarities, there are also important differences among each of these three requirements and practices. For these reasons, most financial institutions in the United States are still providing and managing them separately. This obviously creates a strain on internal staff and resources. One of our clients had an initial compliance strategy in place but did not have the sufficient in-house staff and resources required to create, document and review its modeling and stress testing to satisfy regulators and internal auditors. The organization needed a consultant that could work closely with its in-house team to support sophisticated models that were tailored to meet its specific compliance obligations. We worked closely with the client’s team to provide extensive consulting support for a complex set of loss-forecasting models and other tools, applying industry best practices to fully document the models. Throughout the process, our consulting team discovered and identified content gaps to help ensure that all documentation was complete. We also provided ad hoc analytics to support the client’s model development effort and strategic and tactical guidance on stress testing model development for compliance. This enabled the client to develop primary and challenge models for DFAST’s CCAR requirements, as well as internal stress scenarios. It also provided the client with the following tangible business benefits: balance compliance with maximum profitability and revenue; provided knowledge sharing and best practices to help empower client employees; helped refine models based on feedback from internal and external governance organizations; supported models with academic research to help align the correct model to the correct processes; and provided assistance with model implementation and application. Click here for a recent video I did on how capital-adequacy positions are becoming crucial in analyst recommendations.

Increased volume of fraud attempts during back to school shopping season Back to school shopping season will be the first time many consumers' use their chip-enabled credit cards and stores' new card readers. With the average K-12 family spending $630.36 per child in back to school shopping, and more than 1/3 shopping online, according to the National Retail Federation - is your fraud strategy prepared to handle the increased volume? And are you using a dynamic knowledge based authentication (KBA) solution that incorporates a wide variety of questions categories as part of your multi-faceted risk based authentication approach to fraud account management? Binary verification, or risk segmentation based on a single pass/fail decision is like trying to stay dry in a summer rain storm by wearing a coat. It’s far more effective to wear rubber boots and a use an umbrella, in addition to wearing a rain coat. Binary verification can occur based on evaluating identity elements with two outcomes –pass or fail – which could leave you susceptible to a crafty fraudster. When we recommend a risk based authentication approach, we take a more holistic view of a consumers risk profile. We advocate using analytics and weighting many factors, including identity elements, device intelligence and a robust knowledge-based authentication solution that work in concert to provide overall risk based decision. After all, the end-goal is to enable the good consumers to continue forward based, while preventing the fraudster from compromising your customer’s identity and infiltrating you’re your business.

Imagine the following scenario: an attacker acquires consumers’ login credentials through a data breach. They use these credentials to test account access and observe account activity to understand the ebbs and flows of normal cash movement – peering into private financial records – verifying the optimal time to strike for the most financial gain. Surveillance and fraud staging are the seemingly benign and often-transparent account activities that fraudsters undertake after an account has been compromised but before that compromise has been detected or money is moved. Activities include viewing balances, changing settings to more effectively cover tracks, and setting up account linkages to stage eventual fraudulent transfers. The unfortunate thing is that the actual theft is often the final event in a series of several fraudulent surveillance and staging activities that were not detected in time. It is the activity that occurs before theft that can severely undermine consumer trust and can devastate a brand’s reputation. Read more about surveillance, staging and the fraud lifecycle in this complimentary whitepaper.

Understanding shelf companies and shell companies In our world of business challenges with revenues level or trending down and business loans tougher than ever to get, “shelf” and “shell” companies continue to be an easy option for business opportunities. Shelf companies are defined as corporations formed in a low-tax, low-regulation state in order to be sold off for its excellent credit rating. Click on the internet and you will see a plethora of vendors selling companies in a turn-key business packages. Historically off-the-shelf structures were used to streamline a start-up, where an entrepreneur instantly owns a company that has been in business for several years without debt or liability. However, selling them as a way to get around credit guidelines is new, making them unethical and possibly illegal. Creating companies that impersonate a stable, well established companies in order to deceive creditors or suppliers in another way that criminals are using shelf companies for fraudulent use. Shell companies are characterized as fictitious entities created for the sole purpose of committing fraud. They often provide a convenient method for money laundering because they are easy and inexpensive to form and operate. These companies typically do not have a physical presence, although some may set up a storefront. According to the U.S. Department of the Treasury’s Financial Crimes Enforcement Network, shell companies may even purchase corporate office “service packages” or “executive meeting suites” in order to appear to have established a more significant local presence. These packages often include a state business license, a local street address, an office that is staffed during business hours, a conference room for initial meetings, a local telephone listing with a receptionist and 24-hour personalized voice mail. In one recent bust out fraud scenario, a shell company operated out of an office building and signed up for service with a voice over Internet protocol (VoIP) provider. While the VoIP provider typically conducts on-site visits to all new accounts, this step was skipped because the account was acquired through a channel partner. During months one and two, the account maintained normal usage patterns and invoices were paid promptly. In month three, the account’s international toll activity spiked, causing the provider to question the unusual account activity. The customer responded with a seemingly legitimate business explanation of activity and offered additional documentation. However, the following month the account contact and business disappeared, leaving the VoIP provider with a substantial five figure loss. A follow-up visit to the business showed a vacant office suite. While it’s unrealistic to think all shelf and shell companies can be identified, there are some tools that can help you verify businesses, identify repeat offenders, and minimize fraud losses. In the example mention above, post-loss account review through Experian’s BizID identified an obvious address discrepancy – 12 businesses all listed at the same address, suggesting that the perpetrator set up numerous businesses and victimized multiple organizations. It is possible to avoid being the next victim and refine and revisit your fraud best practices today. Learn more about Experian BizID and how to protect your business.
Apple eschewed banks for a retailer focus onstage at their Worldwide Developers Conference (WWDC) when it spoke to payments. I sense this is an intentional shift – now that stateside, you have support from all four networks and all the major issuers – Apple understands that it needs to shift the focus on signing up more merchants, and everything we heard drove home that note. That includes Square’s support for NFC, as well as the announcements around Kohls, JCPenney and BJ’s. MasterCard's Digital Enablement Service (MDES) - opposite Visa’s Token Service - is the tokenization service that has enabled these partnerships specifically through MasterCard’s partners such as Synchrony – (former GE Capital) which brought on JCPenney, Alliance Data which brought on BJ’s, and CapitalOne which enabled Kohls. Within payments common sense questions such as: “Why isn’t NFC just another radio that transmits payment info?” or “Why aren’t retailer friendly payment choices using NFC?” have been met with contemptuous stares. As I have written umpteen times (here), payments has been a source of misalignment between merchants and banks. Thus – conversations that hinged on NFC have been a non-starter, for a merchant that views it as more than a radio – and instead, as a trojan horse for Visa/MA bearing higher costs. When Android opened up access to NFC through Host Card Emulation (HCE) and networks supported it through tokenization, merchants had a legitimate pathway to getting Private label cards on NFC. So far, very few indeed have done that (Tim Hortons is the best example). But between the top two department store chains (Macy’s and Kohls) – we have a thawing of said position, to begin to view technologies pragmatically and without morbid fear. It must be said that Google is clearly chasing Apple on the retailer front, and Apple is doing all that it can, to dig a wider moat by emphasizing privacy and transparency in its cause. It is proving to be quite effective, and Google will have to “apologize beforehand” prior to any merchant agreement – especially now that retailers have control over which wallets they want to work with – and how. This control inherits from the structures set alongside the Visa and MasterCard tokenization agreements – and retailers with co-brand/private label cards can lean on them through their bank partners. Thus, Google has to focus on two fronts – first to incentivize merchants to partner so that they bring their cards to Android Pay, while trying to navigate through the turbulence Apple has left in its wake, untangling the “customer privacy” knot. For merchants, at the end of the day, the questions that remain are about operating costs, and control. Does participation in MDES and VEDP tokenization services through bank partners, infer a higher cost for play – for private label cards? I doubt if Apple’s 15bps “skim off the top” revenue play translates to Private Label, especially when Apple’s fee is tied to “Fraud Protection” and Fraud in Private Label is non-existent due to its closed loop nature. Still – there could be an acquisitions cost, or Apple may plan a long game. Further, when you look at token issuance and lifecycle management costs, they aren’t trivial when you take in to context the size of portfolio for some of these merchants. That said, Kohls participation affords some clarity to all. Second, Merchants want to bring payments inside apps – just like they are able to do so through in-app payments in mobile, or on online. Forcing consumers through a Wallet app – is counter to that intent, and undesirable in the long scheme. Loyalty as a construct is tangled up in payments today – and merchants who have achieved a clean separation (very few) or can afford to avoid it (those with large Private label portfolios that are really ‘loyalty programs w/ payments tacked on’) – benefit for now. But soon, they will need to fold in the payment interaction in to their app, or Apple must streamline the clunky swap. The auto-prompt of rewards cards in Wallet is a good step, but that feels more like jerry rigging vs the correct approach. Wallet still feels very v1.5 from a merchant integration point of view. Wallet not Passbook. Finally, Apple branding Passbook to Wallet is a subtle and yet important step. A “bank wallet” or a “Credit Union wallet” is a misnomer. No one bank can hope to build a wallet – because my payment choices aren’t confined to a single bank. And even where banks have promoted “open wallets” and incentivized peers to participate – response has been crickets at best. On the flip side, an ecosystem player that touches more than a device, a handful of experiential services in entertainment and commerce, a million and a half apps – all with an underpinning of identity, can call itself a true wallet – because they are solving for the complete definition of that term vs pieces of what constitutes it. Thus – Google & Apple. So the re-branding while being inevitable, finds a firm footing in payments, looks toward loyalty and what lies beyond. Solving for those challenges has less to do with getting there first, but putting the right pieces in play. And Apple’s emphasis (or posturing – depending on who you listen to) on privacy has its roots in what Apple wants to become, and access, and store on our behalf. Being the custodian of a bank issued identity is one thing. Being a responsible custodian for consumer’s digital health, behavior and identity trifecta has never been entirely attempted. It requires pushing on all fronts, and a careful articulation of Apple’s purpose to the public must be preceded by the conviction found in such emphasis/posturing. Make sure to read our perspective paper to see why emerging channels call for advanced fraud identification techniques

By: Mike Horrocks The other day in the American Banker, there was an article titled “Is Loan Growth a Bad Idea Right Now?”, which brings up some great questions on how banks should be looking at their C&I portfolios (or frankly any section of the overall portfolio). I have to admit I was a little down on the industry, for thinking the only way we can grow is by cutting rates or maybe making bad loans. This downer moment required that I hit my playlist shuffle and like an oracle from the past, The Clash and their hit song “Should I stay or should I go”, gave me Sage-like insights that need to be shared. First, who are you listening to for advice? While I would not recommend having all the members of The Clash on your board of directors, could you have maybe one. Ask yourself are your boards, executive management teams, loan committees, etc., all composed of the same people, with maybe the only difference being iPhone versus Android?? Get some alternative thinking in the mix. There is tons of research to show this works. Second, set you standards and stick to them. In the song, there is a part where we have a bit of a discussion that goes like this. “This indecision's buggin' me, If you don't want me, set me free. Exactly whom I'm supposed to be, Don't you know which clothes even fit me?” Set your standards and just go after them. There should be no doubt if you are going to do a certain kind of loan or not based on the pricing. Know your pricing, know your limits, and dominate that market. Lastly, remember business cycles. I am hopeful and optimistic that we will have some good growth here for a while, but there is always a down turn…always. Again from the lyrics – “If I go there will be trouble, An' if I stay it will be double” In the American Banker article, M&T Bank CFO Rene Jones called out that an unnamed competitor made a 10-year fixed $30 million dollar loan at a rate that they (M&T) just could not match. So congrats to M&T for recognizing the pricing limits and maybe congrats to the unnamed bank for maybe having some competitive advantage that allowed them to make the loan. However if there is not something like that supporting the other bank…the short term pain of explaining slower growth today may seem like nothing compared to the questioning they will get if that portfolio goes south. So in the end, I say grow – soundly. Shake things up so you open new markets or create advantages in your current market and rock the Casbah!
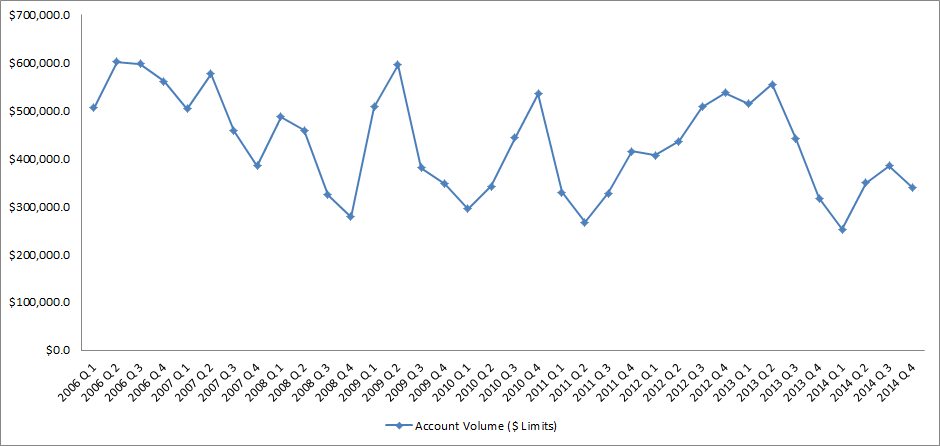
Source: IntelliViewsm powered by Experian Sales of existing homes dropped 50% from the peak in August 2005 to the low point in July 2010. The spike in home sales in late 2009 and early 2010 was due to the large number of foreclosure sales as well as very low prices. Since 2010, sales have increased to almost to the level they were in 2000, before the financial crisis. However, the homeownership rate has steadily gone down. How could sales have picked up while the homeownership rate declined? Investors have entered the market snapping up single family homes and renting them. Therefore, the recent good news in the existing home market has been driven by investors, not homeowners. But as I point out below, this is changing. Looking at the homeownership rate by age, shown in the table below, it is clear that since the crisis the rate has declined most for people under 45. The potential for marketing is greatest in this cohort as the numbers indicate a likely demand for housing. Homeownership Rate by Age Source: U.S. Census Bureau and Haver Analytics as reported on the Federal Reserve Bank of St. Louis Fred database The factors that have impeded growth, described above, are beginning to reverse which, along with pent-up demand, will present an opportunity for mortgage originators in 2015. Home prices have risen in 246 of the 277 cities tracked by Clear Capital.With prices going up, investors have begun to back away from the market, resulting in prices increasing at a slower rate in some cities but they are still increasing.Therefore the perception that homeownership is risky will likely change.In fact, in some areas, such as California’s coastal cities, sales are strong and prices are going up rapidly. Lenders and regulators are recognizing that the stringent guidelines put in place in reaction to the crisis have overly constrained the market.Fannie Mae and Freddie Mac are reducing down payment requirements to as low as 3%.FHA is lowering their guarantee fee, reducing the amount of cash buyers need to close transactions.Private securitizations, which dried up completely, are beginning to reappear, especially in the jumbo market. As unemployment continues to go down, consumer confidence will rise and household formation will return to more normal levels which result in more sales to first time homebuyers, who drive the market.According to Lawrence Yun, chief economist for the National Association of Realtors, “…it’s all about consistent job growth for a prolonged period, and we’re entering that stage.” The number of houses in foreclosure, according to RealtyTrac, has fallen to pre-crisis levels.This drag on the market has, for the most part, cleared and as prices continue to inflate, potential buyers will be motivated to buy before homes become unaffordable.Despite the recent increases, home prices are still, on average, 23% lower than they were at the peak. Focusing marketing dollars on those people with the highest propensity to buy has always been a challenge but in this market there are identifiable targets. “Boomerangs” are people who owned real estate in the past but are currently renting and likely to come back into the market.Marketing to qualified former homeowners would provide a solid return on investment. People renting single family houses are indicating a lifestyle preference that can be marketed to. Newly-formed households are also profitable targets. The housing market, at long last, appears to be finally turning the corner and normalizing. Experian’s expertise in identifying the right consumers can help lenders to pinpoint the right people on whom marketing dollars should be invested to realize the highest level of return. Click here to learn more.