All posts by Guest Contributor

There are two core fundamentals of evaluating loan loss performance to consider when generating organic portfolio growth through the setting of customer lending limits. Neither of which can be discussed without first considering what defines a “customer.” Definition of a customer The approach used to define a customer is critical for successful customer management and is directly correlated to how joint accounts are managed. Definitions may vary by how joint accounts are allocated and used in risk evaluation. It is important to acknowledge: Legal restrictions for data usage related to joint account holders throughout the relationship Impact on predictive model performance and reporting where there are two financially linked individuals with differently assigned exposures Complexities of multiple relationships with customers within the same household – consumer and small business Typical customer definitions used by financial services organizations: Checking account holders: This definition groups together accounts that are “fed” by the same checking account. If an individual holds two checking accounts, then she will be treated as two different and unique customers. Physical persons: Joint accounts allocated to each individual. If Mr. Jones has sole accounts and holds joint accounts with Ms. Smith who also has sole accounts, the joint accounts would be allocated to both Mr. Jones and Ms. Smith. Consistent entities: If Mr Jones has sole accounts and holds joint accounts with Ms. Smith who also has sole accounts, then 3 “customers” are defined: Jones, Jones & Smith, Smith. Financially-linked individuals: Whereas consistent entities are considered three separate customers, financially-linked individuals would be considered one customer: “Mr. Jones & Ms. Smith”. When multiple and complex relationships exist, taking a pragmatic approach to define your customers as financially-linked will lead to a better evaluation of predicted loan performance. Evaluation of credit and default risk Most financial institutions calculate a loan default probability on a periodic basis (monthly) for existing loans, in the format of either a custom behavior score or a generic risk score, supplied by a credit bureau. For new loan requests, financial institutions often calculate an application risk score, sometimes used in conjunction with a credit bureau score, often in a matrix-based decision. This approach is challenging for new credit requests where the presence and nature of the existing relationship is not factored into the decision. In most cases, customers with existing relationships are treated in an identical manner to those new applicants with no relationship – the power and value of the organization’s internal data goes overlooked whereby customer satisfaction and profits suffer as a result. One way to overcome this challenge is to use a Strength of Relationship (SOR) indicator. Strength of Relationship (SOR) indicator The Strength of Relationship (SOR) indicator is a single-digit value used to define the nature of the relationship of the customer with financial institution. Traditional approaches for the assignment of a SOR are based upon the following factors Existence of a primary banking relationship (salary deposits) Number of transactional products held (DDA, credit cards) Volume of transactions Number of loan products held Length of time with bank The SOR has a critical role in the calculation of customer level risk grades and strategies and is used to point us to the data that will be the most predictive for each customer. Typically the stronger the relationship, the more we know about our customer, and the more robust will be predictive models of consumer behavior. The more information we have on our customer, the more our models will lean towards internal data as the primary source. For weaker relationships, internal data may not be robust enough alone to be used to calculate customer level limits and there will be a greater dependency to augment internal data with external third party data (credit bureau attributes.) As such, the SOR can be used as a tool to select the type and frequency of external data purchase. Customer Risk Grade (CRG) A customer-level risk grade or behavior score is a periodic (monthly) statistical assessment of the default risk of an existing customer. This probability uses the assumption that past performance is the best possible indicator of future performance. The predictive model is calibrated to provide the probability (or odds) that an individual will incur a “default” on one or more of their accounts. The customer risk grade requires a common definition of a customer across the enterprise. This is required to establish a methodology for treating joint accounts. A unique customer reference number is assigned to those customers defined as “financially-linked individuals”. Account behavior is aggregated on a monthly basis and this information is subsequently combined with information from savings accounts and third party sources to formulate our customer view. Using historical customer information, the behavior score can accurately differentiate between good and bad credit risk individuals. The behavior score is often translated into a Customer Risk Grade (CRG). The purpose of the CRG is to simplify the behavior score for operational purposes making it easier for noncredit/ risk individuals to interpret a grade more easily than a mathematical probability. Different methods for evaluating credit risk will yield different results and an important aspect in the setting of customer exposure thresholds is the ability to perform analytical tests of different strategies in a controlled environment. In my next post, I’ll dive deeper into adaptive control, champion challenger techniques and strategy design fundamentals. Related content: White paper: Improving decisions across the Customer Life Cycle

By: Joel Pruis So we know we need to determine the overall net yield on assets required to cover the cost of funds and the operating expenses but how? In the movie Moneyball, the Oakland A’s develop a strategy to win 99 games by scoring 814 runs and only allowing 645 runs by the opposition. In order to generate the necessary runs, Peter Brand boils down all the stats into one number, on base percentage. By looking at the on-base percentage of all the players in the league, Brand is able to determine the likelihood of generating runs. There are a few key phrases/quotes from this scene that need to be highlighted: “it’s about getting things down to one number” “People are overlooked for a variety of biased reasons and ‘perceived’ flaws.” “Bill James and mathematics cut straight through that [biased reasons and perceived flaws].” Getting things down to one number is the liberating element for the Oakland A’s and for banking. We have already identified the one number for banking – Net Yield on Assets. Let’s define this a bit further though. For this exercise, net yield means the gross yield (interest income plus fee income) on assets less charge offs. We are looking to see what is going to be the consistent return on the assets less what can be expected net charge off related to the assets. When Billy Beane and Peter Brand got it down to the one number “On Base Percentage” it altered the player selection process and highlighted the biases of the scouts such as: Giambi’s brother was “getting a little thick around the waist” “Old Man” Justice Justice will be “lucky if he hits his weight” in July and August Justice’s “legs are gone Hatteberg “can’t throw” Hatteberg’s “best part of his career is over” Hatteberg “walks a lot” None of the above comments used any facts or data to disprove each player’s on base percentage. Can you imagine if they were underwriters or lenders? What type of compliance issues would we have on our hands with the above comments? Biased against disabilities (Hatteberg with nerve damage); Age Discrimination (“Old Man” Justice), Physical Appearance (Giambi’s brother “getting a little thick around the waist”), these scouts would be a compliance liability let alone obstacles in any type of organizational change. But one can readily see how focusing on one number liberates the thinking and removes the old constraints or ways of thinking. One of the scouts commented that Hatteberg had a high on base percentage because he walks a lot, considering a walk as a negative while a hit is a positive but why? Why is getting on base by being walked a negative but getting on base with a hit is positive? The result is the same as the movie points out. How about in commercial lending? If we focus on net yield on the portfolio as the one number, does that do anything to remove biases? I believe that it does. One example is the perception of charge offs in a portfolio. To this day the notion of a charge off in a commercial portfolio, even in the small business portfolio, is frowned upon and can jeopardize one’s career. Similar to the walk, the charge off is not desired but if we focus on the one number, net yield, it actually removes the stigma of the charge off! If we need at minimum a 6% net asset yield and we are able to generate a gross yield of 9% with an expected loss rate of 2%, we actually exceed our “one number” of a targeted net yield of 6% with an expected net yield of 7%. With that change that removes the biases and flawed perception, can we now start to find opportunities that provide us with the ability to step away from the norm; stop competing with the rest; and generate that higher return that is required? What are the potential biases and flawed perceptions that will need to be addressed? “High Risk” Industries? “Undesired” Loan types? Consumer vs. Commercial? Real Estate Secured vs. Unsecured? Loans vs. Treasuries or other earning asset types? But just as in the movie, you need to be prepared for the response you may get from the traditional ‘seasoned’ lenders in your organization. When Billy Beane puts the new strategy into place at the Oakland A’s, the lead scout responds with: “You don’t put a team together with a computer” “Baseball isn’t just numbers, it isn’t science. If it was anybody could do what we do but they can’t.” “They don’t know what we know. They don’t have our experience and they don’t have our intuition.” Ah, just like the traditional baseball scout is the traditional commercial lender with the years of experience, judgment and intuition. I used to be one and used almost word for word the same argument against credit scoring and small business before I truly understood what it was all about. Don’t get me wrong. Experience, judgment and intuition is valuable and necessary. But that type of judgment tends to get into trouble when it stops looking outside for data and only relies on past personal experience to assess the next moves. Experience is always important but it has to continually review, assess and interpret the data. So let’s start looking at the different types of data. On deck – How do we know how many runs the opposition is going to score? The use of external data.

By: Joel Pruis I am going to take some liberties here. Nowhere in the movie Moneyball does Peter Brand tell us how he got to the magic number of winning 99 games to get to the playoffs. My assumption is that given the way that he evaluates the Oakland A’s, he also evaluations the other teams in their conference. Assessing the competitive landscape provides Brand with the estimated runs their opponents will generate. Now we could take the approach that such analysis would correlate to assessing how your competition is going to perform but I am going to take a different approach. I would compare the conference assessment in Moneyball to be similar to an economic forecast/assessment. We need to assess what are the overall conditions in which we must operate that will allow us to generate the net yield on the assets of our financial institution. Some of the things we need to assess to determine what we will be able to generate related to the net yield on assets would be: Gross yield on assets Current interest rate environment (yield on treasuries, federal home loan bank, etc. Interest rate trends (increasing, declining, trends toward fixed rates, variable rates) Industry information General trend of businesses across the nation How are businesses faring? How well are they paying their creditors? Are they relying more or less on credit? Are new businesses being started? Are they succeeding? Are they failing? General trends (same as above) within your financial institution’s market footprint One such source of the industry information is the Small Business Credit Index generated by Experian & Moody’s Analytics. In the recent release of the Small Business Credit Index, small business is indicating stronger from the prior quarter moving from 104.3 to 109. But this is from a national perspective. Depending on your financial institution, it is important to always get an overall view of the economy but more importantly, what is happening in your particular market footprint. Just as the Oakland A’s in Moneyball maintained an overall perspective of Major League Baseball, their focus for success was targeting their specific conference to reach the playoffs. So as we look at information such as the Small Business Credit Index, we are able to see highlights of regional trends (certain states west of the Mississippi are doing better while certain states along the east coast are not) and specific industry trends. From such data we need to drill down into our specific footprint and current portfolio. We need to review such items as: What industry concentrations do we have that are doing well in the economy and how is our portfolio doing compared to the external data? What industries are we not engaging that may provide a good opportunity for our financial institution? What changes are taking place in the general economy that may impact our ability to achieve our expected results? What external factors must we be monitoring that may impact our strategy (such as the impact of Obamacare and how it will impact the hiring for businesses with more than 50 employees?) Just as in Moneyball, Brand continues to monitor the performance of the overall league (and the individual players for future trades), we need to continually monitor the national, state and local economies to determine what adjustments we will need to make to achieve our strategies. So we have assessed the general environment, on to strategies or “How do we win 99 games with a total payroll of $38 million?”
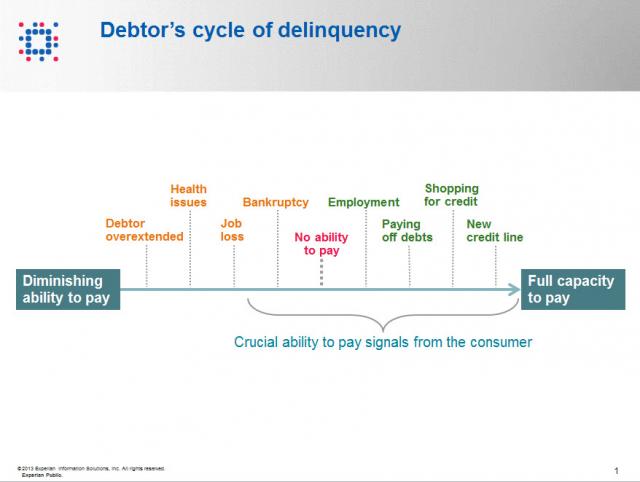
Contact information such as phone numbers and addresses are fundamental to being able to reach a debtor, but knowing when to reach out to the debtor is also a crucial factor impacting success or failure in getting payment. As referenced in the chart below, when a consumer enters the debtor life cycle, they often avoid talking with you about the debt because they do not have the ability to pay. When the debtor begins to recover financially, you want to be sure you are among the first to reach out to them so you can be the first to be paid. According to Don Taylor, President of Automated Collection Services, they have seen a lift of more than 12% of consumers with trigger hits entering repayment, and this on an aged portfolio that has already been actively worked by debt collection staff. Monitoring for a few key changes on the credit profiles of debtors provides the passive monitoring that is needed to tell you the optimal time to reach back to the consumer for payment. Experian compiled several recent collection studies and found that a debtor paying off an account that was previously past due provided a 710% increase in the average payment. Positive improvement on a consumers’ credit profile is one of those vital indicators that the consumer is beginning to recover financially and could have the will—and ability—to pay bad debts. The collection industry is not like the big warehouse stores—quantity and value do not always work hand in hand for the debt collection industry. Targeting the high value credit events that are proven to increase collection amounts is the key to value, and Experian has the expertise, analytics and data to help you collect in the most effective manner. Be sure to check out our other debt collection blog posts to learn how to recover debt more quickly and efficiently.

By: Joel Pruis What is it we as bankers are trying to accomplish? If you have been in the industry for 20+ years, this question may sound ridiculous! We do what we do! We are bankers! What do you mean define what are we trying to do? But that is the question, what is it we are trying to do? I am going to propose we boil it down to the basic/fundamental element – Banks aggregate money from various sources and redeploy these funds to earn a return for the shareholders. Ultimately, our objective is to generate an appropriate return for the shareholders Getting back to the movie Moneyball, Billy Beane and Peter Brand define the objective of the Oakland A’s for the season in terms of projecting the number of wins that are needed to assure, with all probability, that the team makes the playoffs (this would be similar to the objective of banking to generate an appropriate return for the shareholders). But Peter Brand quickly moves into very specific targets that are required for the A’s to make it to the playoffs, namely win 99 regular season games. In order to win 99 regular season games, the A’s offense will need to score 814 runs in the season and defensively only allow 645 runs. Plain and simple. Very objective, very measurable and it is all based upon data, data, data. Let’s break this down. Based upon their conference, the teams in their conference along with the overall schedule, Peter Brand projects that 99 wins are necessary to land a spot in the playoffs. No gut check, no darts or crystal ball but rather historical data that when analyzed provides the benchmark of 99 wins to statistically assure the Oakland A’s that they will make the playoffs. So let’s apply this to banking. Our objective is to generate the appropriate return for our shareholders or the old Return on Equity. So, for example, if our targeted return on equity is 20% (making the playoffs) we need to make sure we generate enough net income (99 wins) through producing the necessary gross yield on assets (814 runs generated by the Oakland A’s offense) less the expected charge offs (645 runs allowed by the Oakland A’s defense). For a quick dive into details, our data would provide for a margin of error on the variable to provide for statistical assurance of achieving the objective (Return on Equity). In the movie there is no guaranty that the 814 runs will win the conference but at the same time there is no guaranty that the Oakland A’s opponents will score 645 runs. Never in the movie does the coach, Billy Beane or Peter Brand tell the team, “You only have to score X number of runs this game, don’t score anymore.” Or even crazier, “You are not letting the other team score enough runs, they need to score 645!” No, the strategy is still to generate as many runs as possible while minimizing the number of runs scored by the opposition. Rather it is the review of the total amount of earning assets of the financial institution and the overall credit quality that we must understand and control to determine our ability to generate the net yield on assets required to generate the return on equity that is required. If we assume too much risk in the portfolio in order to generate the required yield it would be similar to having a poor pitching staff projected to allow 10 runs a game requiring the team to produce 11 runs a game in order to win. It just is not realistic. So basically we need to assess at the high level, are we appropriately structured to allow for the generation of enough profit to provide the appropriate return on equity. At this point, we do not need to complicate it any further than that. Now let’s take a look at the constraints. We know we have them in banking, let’s take a look at probably the single biggest constraint imposed on Billy Beane and the Oakland A’s. In the movie, before Billy Beane is even aware of the Moneyball concept, his is given his constraint by the owner. Beane asks for more money to ‘buy players’ and is flat out rejected by the owner. The owner, in fact, cuts Beane off by asking, “is there anything else I can do for you?”. Net result is that the Oakland A’s have $38 million dollars for payroll vs. the New York Yankees at $120 million. Seriously it does not seem fair. How can you attract the needed talent when you cannot pay the type of salary needed to get the necessary players to win a championship? Let’s rephrases this for banking… How can a bank be expected to deploy its assets when such a high rate of return is required? Boiling it down to a specific example, “How can I originate a commercial loan at this rate of interest when the competition is ½ to 1% lower than our rates?” Up next – Why will 99 games get us to the playoffs? How do we assess the environment?

By: Joel Pruis Times are definitely different in the banking world today. Regulations, competition from other areas, specialized lenders, different lending methods resulting in the competitive landscape we have today. One area that is significantly different today, and for the better, is the availability of data. Data from our core accounting systems, data from our loan origination systems, data from the credit bureaus for consumer and for business. You name it, there is likely a data source that at least touches on the area if not provides full coverage. But what are we doing with all this data? How are we using it to improve our business model in the banking environment? Does it even factor into the equation when we are making tactical or strategic decisions affecting our business? Unfortunately, I see too often where business decisions are being made based upon anecdotal evidence and not considering the actual data. Let’s take, for example, Major League Baseball. How much statistics have been gathered on baseball? I remember as a boy keeping the stats while attending a Detroit Tigers game, writing down the line up, what happened when each player was up to bat, strikes, balls, hits, outs, etc. A lot of stats but were they the right stats? How did these stats correlate to whether the team won or lost, does the performance in one game translate into predictable performance of an entire season for a player or a team? Obviously one game does not determine an entire season but how often do we reference a single event as the basis for a strategic decision? How often do we make decisions based upon traditional methods without questioning why? Do we even reference traditional stats when making strategic decisions? Or do we make decisions based upon other factors as the scouts of the Oakland A’s were doing in the movie Moneyball? In one scene of the Movie, Billy Beane, general manager of the A’s, is asking his team of scouts to define the problem they are trying to solve. The responses are all very subjective in nature and only correlate to how to replace “talented” players that were lost due to contract negotiations, etc. Nowhere in this scene do any of the scouts provide any true stats for who they want to pursue to replace the players they just lost. Everything that the scouts are talking about relates to singular assessments of traits that have not been demonstrated to correlate to a team making the playoffs let alone win a single game. The scouts with all of their experience focus on the player’s swing, ability to throw, running speed, etc. At one point the scouts even talk about the appearance of the player’s girlfriends! But what if we changed how we looked at the sport of baseball? What if we modified the stats used to compile a team; determine how much to pay for an individual player? The movie Moneyball highlights this assessment of the conventional stats and their impact or correlation to a team actually winning games and more importantly the overall regular season. Bill James is given the credit in the movie for developing the methodology ultimately used by the Oakland A’s in the movie. This methodology is also referred to as Sabermetrics. In another scene, Peter Brand, explains how baseball is stuck in the old style of thinking. The traditional perspective is to buy ‘players’. In viewing baseball as buying players, the traditional baseball industry has created a model/profile of what is a successful or valuable player. Buy the right talent and then hopefully the team will win. Instead, Brand changes the buy from players to buying wins. Buying wins which require buying runs, in other words, buy enough average runs per game and you should outscore your opponent and win enough games to win your conference. But why does that mean we would have to change the way that we look at the individual players? Doesn’t a high batting average have some correlation to the number of runs scored? Don’t RBI’s (runs batted in) have some level of correlation to runs? I’m sure there is some correlation but as you start to look at the entire team or development of the line up for any give game, do these stats/metrics have the best correlation to lead to greater predictability of a win or more specifically the predictability of a winning season? Similarly, regardless of how we as bankers have made strategic decisions in the past, it is clear that we have to first figure out what it is exactly we are trying to solve, what we are trying to accomplish. We have the buzz words, the traditional responses, the non-specific high level descriptions that ultimately leave us with no specific direction. Ultimately it allows us to just continue the business as usual approach and hope for the best. In the next few upcoming blogs, we will continue to use the movie Moneyball as the back drop for how we need to stir things up, identify exactly what it is we are trying to solve and figure out how to best approach the solution.

By: Matt Sifferlen Ah, fraudulent behavior is currently enjoying a bright shiny moment in the sun in today's pop culture, particularly in the world of sports. Whether it's a college athlete being duped for months by telephone conversations with a non-existent girlfriend, or the world's best known cyclist coming clean on a lifetime of deceit, in both cases we're left shaking our heads and laughing, crying, or cringing while telling ourselves "I'm glad I'm too smart to fall for any of this." But are you just kidding yourself? In the case of the college football player, most of us have been scratching our heads wondering how any adult could possibly get strung along for such an extended period of time by such a scam. But if you take a closer look at the interaction between the athlete and the fraudster, you'll see that the fraudster deployed some typical tactics that allowed him to keep the scam living and breathing. In particular, he continuously kept communicating with the athlete via phone and social media, reinforcing the perception that he's aboveboard and genuinely interested in the athlete's life. We see this in commercial fraud interactions too, where the commercial fraudster will perform expected, normal tasks and activities (e.g. making small payments on loans, placing phone calls to lender support staff) that will reinforce the lender's perception that the fraudster is just another normal client. But unlike the athlete's scenario where the fraudster's story unraveled due to no logical conclusion being planned, commercial fraudsters will string lenders along until they get what they want -- then they vanish. Lenders can't get too complacent in their fraud prevention efforts, assuming that the mere presence of normal account activity equates to a validation of a client's authenticity. To complicate things, while electronic communication methods like text messages, emails, and Twitter or Facebook messages offer many convenience advantages, they are ripe for manipulation by fraudsters who certainly find these methods preferable to any awkward face to face encounters with someone they're victimizing. The cyclist that admitted to a lifetime of lies also shines the light on some other tactics that commercial fraudsters might use -- using perceived image and reputation to deceive. Fraudsters will often steal identities of licensed professionals (think physicians, dentists) with favorable credit profiles and use their information to apply for commercial credit or services, knowing that they will likely be viewed favorably due to their impressive profiles, at least on paper. In today's world where lightly staffed underwriting teams struggle to keep up with their workloads, it's easy to see why this tactic can help increase the odds that an application might escape closer scrutiny. After all, it's a doctor's office so what could possibly go wrong? A lot, if you're approving someone who really isn't the doctor! An objective evaluation and screening process where underwriting and analyst staff consistently verify all applicant data and not just cherry pick the ones that look suspicious on paper can go a long way towards avoiding this typical trap set by commercial fraudsters. And in the final scenario of art imitating life, there is the recent release of a major motion picture comedy about identify theft. I'm sure anyone who has been a victim of identity theft won't find hilarity in the scenes of the victim's life getting turned upside down, suddenly unable to use his credit cards at the gas station and being asked about transactions that took place somewhere else in the country that he's never visited. But undoubtedly many folks will find this humor hilarious because we probably know of some horror story that a friend or acquaintance has shared with us that is similar to one of the wacky scenarios covered in this movie. So we'll laugh and take comfort in the fact that we're too smart to get scammed like this, but if the FTC is stating that identity theft will affect 1 in 6 people each year then we're fooling ourselves in thinking that our number won't be up at some point soon. So what can be learned from these high profile pop culture events? I think a couple things. First, know your customers (or athletes, heroes, girlfriends). It sounds simple, but make sure they are who they say they are. Whether you're lending to a business or a consumer, there are tools out there that can enable you to objectively screen your applicants and minimize any bias that might get exploited by fraudsters in a manual review heavy process. If you're not cautious and get burnt, you might not have to go on Oprah or Dr. Phil to explain to your management team where things went horribly wrong, but the level of financial and reputational damage inflicted could be a painful lesson for you and your institution. Or if you're really (un)lucky, maybe they'll make a movie about your story -- wouldn't that be hilarious? (sarcasm intended)

The purpose of any type of insurance is to protect your most valuable assets. To combat the prevalence of cyber attacks and data breaches, an increasing number of businesses in the health-care, financial services and technology industries have purchased cyber insurance policies to protect themselves from the crippling cost of a data breach. This is especially popular among start-up tech companies in Silicon Valley in order to safeguard their intellectual property (IP) since their IP is the backbone of their livelihood1. Since small businesses generally don’t have a risk manager and IT department dedicated to data security, a good cyber insurance policy can help mitigate cyber security risks. Although accepted in some sectors, cyber insurance is still not an established part of many companies’ IT data security strategies. This is commonly due to a lack of agreed risk management standards and the challenge of substantiating and quantifying losses, in addition to finding objective data to back up cyber insurance claims. Some security experts feel that the federal government needs to kick start growth in this market by requiring government contractors to purchase cyber insurance to set a standard for other businesses, sending a message that any company who has cyber security insurance is a signal that the company is competently managing its data security. As the cyber insurance industry evolves, here is a list of what the policies generally cover and what to look for: First-party claims – Costs incurred by the loss of trade secrets and intellectual property. Third-party claims – Damages a business must pay to customers who sue them for lost or compromised personal information. Business interruption coverage – In the event a data breach incident prevents the company from operating or functioning, the company would receive payment reimbursement for expenses incurred due to loss of business. A forensic IT investigation – Policies can cover the cost of an examination into how the data breach occurred and some may even cover the costs of regulatory fines and penalties in addition to the crisis management control which includes data breach notification letters. Security professionals stress that cyber insurance is not meant to be a substitute for data protection and security policies. In fact, before underwriting a policy, an insurance company will be hyper vigilant in determining that their customers have proper protections and policies in place since the insurance company will want to reduce its own risk. And since insurance has been a positive influence on other industries to improve performance and safety due to risk mitigation, the theory is if a company has cyber insurance, the hope is they will implement proper preventative measures to ensure that they will never have to use it. Learn more about our Data Breach solutions 1http://www3.cfo.com/article/2013/4/data-security_cyber-attacks-cybersecurity-liability-insurance-smb-growth-companies-risk-hogan-lovells

By: Maria Moynihan Cybersecurity, identity management and fraud are common and prevalent challenges across both the public sector and private sector. Industries as diverse as credit card issuers, retail banking, telecom service providers and eCommerce merchants are faced with fraud threats ranging from first party fraud, commercial fraud to identity theft. If you think that the problem isn't as bad as it seems, the statistics speak for themselves: Fraud accounts for 19% of the $600 billion to $800 billion in waste in the U.S. healthcare system annually Medical identity theft makes up about 3% of 8.3 million overall victims of identity theft In 2011, there were 431 million adult victims of cybercrime in 24 countries In fiscal year 2012, the IRS’ specialized identity theft unit saw a 78% spike from last year in the number of ID theft cases submitted The public sector can easily apply the same best practices found in the private sector for ID verification, fraud detection and risk mitigation. Here are four sure fire ways to get ahead of the problem: Implement a risk-based authentication process in citizen enrollment and account management programs Include the right depth and breadth of data through public and private sources to best identity proof businesses or citizens Offer real-time identity verification while ensuring security and privacy of information Provide a Knowledge Based Authentication (KBA) software solution that asks applicants approved random questions based on “out-of-wallet” data What fraud protection tactics has your organization implemented? See what industry experts suggest as best practices for fraud protection and stay tuned as I share more on this topic in future posts. You can view past Public Sector blog posts here.

By: Lloyd Parker Another Experian Vision Conference comes to a close today but not without a full morning of breakout sessions with compelling speakers and experts sharing real-world strategies for real opportunity and real growth. The conference concluded with an entertaining and thought-provoking speaker, Sir Ken Robinson, Ph.D., author of The Element: How Finding Your Passion Changes Everything and Out of our Minds: Learning to Be Creative, who shared with us ideas on how to cultivate innovation and change within organizations in order to grow with their environments and continue to thrive. We’d like to thank you for making this year’s event one of the best. And thank you for the confidence you give us all year round. We know the great responsibility that goes along with that and we are committed to helping your business succeed. Top Tweets of the Week #Vision2013 the slowest growing loan segment (actually it is negative) is HELOC @cumagazine@dougbenzine at -8% YOY.#engage — Mike Horrocks (@mikehorrocks) May 8, 2013 #vision2013 great credit union discussion at experian conference! — Doug Benzine (@DougBenzine) May 8, 2013 #Vision2013 @sirkenrobinson (1) we are living in a time of revolution (2) we have to think differently about talents (3) then act different — Mike Horrocks (@mikehorrocks) May 8, 2013 'Most adults don't know what their true aptitudes are' Sir Ken Robinson #vision2013 — Michele Raneri (@MLRaneri) May 8, 2013 #Vision2013 @sirkenrobinson Our kids are not trains, they are rockets ready to explore and we need to help them only light the fuse. #engage — Mike Horrocks (@mikehorrocks) May 8, 2013

By: Lloyd Parker James W. Paulsen, Ph.D., Chief Investment Strategist at Wells Capital Management kicked off day two at the Experian Vision 2013 Conference with an upbeat economic outlook for 2013 and what it means longer term, for the next generation. Paulsen is nationally recognized for his views on the economy and publishes his own commentary assessing economic and market trends through his newsletter, Economic and Market Perspective. Today he demonstrated to conference attendees how the United States is in a “gear” year and that the “new normal” has been going on for the past 25 years. His optimism predicts that for the next 10 years we’ll see an estimated 3% GDP growth. As mentioned by some on Twitter, “he makes statistics fun.” The morning was followed by more insightful breakout sessions and the launch of a new session format called, “Viewpoints” – fast paced, quick-hitting sessions that highlight new innovations, forward-thinking solutions and product demonstrations designed to satisfy the attendee’s desire to learn more. Networking activities filled the afternoon, and at the time of post the winners of the golf tournament had not yet been announced. Other highlights from the day Viewpoint: The art of portfolio analysis Maintaining a strong commercial portfolio starts with knowledge. In this session, new concepts are introduced and old concepts were questioned as we shared validated intelligence on which commercial triggers are best suited for effective portfolio management. Viewpoint: A 900% return on small-business marketing Here proven approaches were reviewed for targeting existing small-business customers and prospects for deposits and loans using available firmographic data, business credit scores and response models. Viewpoint: Transaction data signals – challenges and opportunities Experian’s R&D Data Lab shared team insights into how underutilized transaction data might be leveraged as well as how to overcome some of the technical and business challenges that arise. Viewpoint: Find time and money in your credit authorization process Attendees learned how to improve decision making and productivity by bringing together multiple sources of credit authorization information in Baker Hill Advisor®. Viewpoint: Commercial fraud – An ounce of prevention is worth a pound of cure Protecting personal identities is commonplace for most businesses. Commercial fraud may not be a primary concern, but one “rare” occurrence could mean a big loss to profits and reputation. Attendees learned how BizID can prevent fraud in business portfolios and help ensure that appropriate preventive measures are taken. Viewpoint: SaaS for intelligent customer decisioning – separating the hype from the reality A stroll down memory lane highlighted the hype and reality of technology over the last several decades and looked at the realities we face that make this space so difficult to predict. Attendees looked at criteria to help them decipher what’s working, what they can do about it and the critical points to focus on when looking at SaaS solutions. Top tweets: "USA is in a GEAR Year" expects 3% growth this year. #vision2013 #finserv — Patricia Hines (@PJHines) May 7, 2013 #Vision2013 @aitegroup 32% of mobile users think mobile is secure & 55% think it is somewhat secure. Banks need to #engage mobile banking. — Mike Horrocks (@mikehorrocks) May 7, 2013 @experianvision "Growth may surpass expectations this year. Confidence is being upwardly adjusted." Dr. James W. Paulsen. #vision2013 — Martha Staten (@Sauconyandsuds) May 7, 2013

By: Maria Moynihan Reduced budgets, quickly evolving technologies, a weakened economy and resource constraints are clearly impacting the Public Sector, but it’s not all doom and gloom. Always with new challenges, come new opportunities. Government agencies must still effectively run programs, optimize processes and find growth in revenue streams. Below you will find the top 5 business challenges facing the Public Sector and municipal utilities today and ways to overcome them: 1. Difficulty finding debtors When asked to name the top challenge to their debt collection processes, governments most often indicate the difficulty in locating debtors whose whereabouts don’t in fact match information they have on hand. Skip tracing with right party contact data is key to finding people or businesses for collections and there are several cost effective ways to do this - either through industry leading tools or by tapping into available sources like voter registration information. 2. Difficulty in prioritizing debt collection efforts When resources are limited, it is critical to not only focus efforts by size, but by likelihood to make contact and access debtors with an ability to pay. Credit and demographic data elements like income, assets, past payment behavior, and age can all be brought together to better identify areas of greater ROI over others. 3. Lack of data available By simply incorporating third-party data and analytics into an established infrastructure, agencies can immediately gain improved insight for efficient decision making. Leverage on-hand data sources to improve understandings of individuals or businesses. 4. Difficulty of incorporating tools to improve debt recovery Governments too often attempt to reduce backlogs by simply trying to accelerate processes that are suboptimal to start with. This is both expensive and unlikely to produce the desired result. In the case of debt collection, success is driven by the tools and processes that allow for refined monitoring, segmentation and prioritization of accounts for improved decisioning. 5. Difficulty in determining to outsource or continue to internally collect While outsourcing to debt collection agencies is always an option, it may not be the most resourceful one, or in some cases, even necessary. Cost to value considerations per effort need to be made by agencies and often, the most effective strategy is to perform minimal efforts internally and to outsource older or skip accounts to third party agencies. What is your agency’s biggest business challenge? See what industry experts suggest as best practices for Public Sector collections or download Experian’s guide to Maximizing Revenue Potential in the Public Sector to learn more.

By: Lloyd Parker There aren’t many things that energize me more than seeing our clients arrive for the Experian Vision 2013 Conference. Industry leaders from all over the world have joined us in Southern California to kick-off a full day of insightful topics. This year’s event sold out in record time and we have many first time attendees taking advantage of the opportunities to network and learn from industry peers. Today began with a welcome from Steve Wagner, President of Consumer Information Services followed by Victor Nichols, Chief Executive Officer, Experian North America and myself, Lloyd Parker, Group President Credit Services. We launched our key theme of Real Strategies, Real Growth, Real Opportunities, discussing the concept of “reality checks.” Reality check #1: Micro-targeting is required Identify market differences Understand your customer segments Adapt to specific needs of your empowered consumers Reality check #2: Managing risk Protect against risks that follow success Keep your door open for good business Focus on operational efficiencies Reality check #3: Optimizing engagement Utilize all the data of each customer Understand all of your customer touch points Manage customer strategies holistically A key theme of the day was the economic, regulatory and political changes impacting our economy and your customers. We had a conversation with Timothy F. Geithner, 75th U.S. Secretary of the Treasury, who shared his experiences as the principal architect of the President’s strategy to avert economic collapse and to reform the financial system. He also discussed international economic challenges and gave us his personal outlook on the economy. The afternoon featured many great speakers and industry experts across many topics that included hearing from many of our regulators on the topic of banking regulations; experts in the area of mobile payments and banking; along with many of our clients who shared their successful programs and experiences working across consumer and commercial portfolios and the customer lifecycle. Other highlights from the day Things overheard at the Roundtable Sessions: “You don’t need extensive touches for small loans, but let go of Excel,” Community bank topics “Loans are milk, deposits are steak,” Issues and opportunities within commercial risk management roles topic “Pent up demand will lead to overall positive auto market conditions near term,” Automotive hot topics “Keeping various systems in synch; Spend time early on implementation to define biz requirements,” Overcoming system operation challenges topic “Marketing to the underserved remains a challenge,” Issues and opportunities in consumer risk management roles topic “Using mobile to go paperless in commercial lending to improve convenience,” Mobile tools for business lending topic Top tweets: #vision2013 "Be relentlessly skeptical. Be humble about what you don't know." Former Secretary Timothy Geithner. — Martha Staten (@Sauconyandsuds) May 6, 2013 Experian CEO to Us bankers on current reg environment. "we have to get in compliance. We have to grow in compliance".#vision2013 — eric haller (@erichaller2) May 6, 2013 Great description of the current environment - "Economic Pinball" Victor Nichols #vision2013 #finserv — Patricia Hines (@PJHines) May 6, 2013 #vision2013.@experiancredit data lab is the "most unique initiative in the industry". The lab lets you #engage w/ untraditional data. — Mike Horrocks (@mikehorrocks) May 6, 2013 Only take risks you can understand, measure, and monitor. CRO round table. #vision2013 — alissa (@adh314) May 6, 2013 The phone is the new wallet. Apps are the new cards. #engage #vision2013 — Andrew Beddoes (@beddoesa712) May 6, 2013

As we prepare to attend next week’s FS-ISAC & BITS Summit we know that the financial services industry is abuzz about massive losses from the ever-evolving attack vectors including DDoS, Malware, Data Breaches, Synthetic Identities, etc. Specifically, the recent $200 million (and counting) in losses tied to a sophisticated card fraud scheme involving thousands of fraudulent applications submitted over several years using synthetic identities. While the massive scale and effectiveness of the attack seems to suggest a novel approach or gap in existing fraud prevention controls, the fact of the matter is that many of the perpetrators could have been detected at account opening, long before they had an opportunity to cause financial losses. Synthetic identities have been a headache for financial institutions for years, but only recently have criminal rings begun to exploit this attack vector at such a large scale. The greatest challenge with synthetic identities is that traditional account opening processes focus on identity verification compliance around the USA PATRIOT Act and FACT Act Red Flags guidance, risk management using credit bureau scores, and fraud detection using known fraudulent data points. A synthetic identity ring simply sidesteps those controls by using new false identities created with data that could be legitimate, have no established credit history, or slightly manipulate elements of data from individuals with excellent credit scores. The goal is to avoid detection by “blending in” with the thousands of credit card, bank account, and loan applications submitted each day where individuals do not have a credit history, where minor typos cause identity verification false positives, or where addresses and other personal data does not align with credit reports. Small business accounts are an even easier target, as third-party data sources to verify their authenticity are sparse even though the financial stakes are higher with large lines of credit, multiple signors, and complex (sometimes international) transactions. Detecting these tactics is nearly impossible in a channel where anonymity is king — and many rings have become experts on gaming the system, especially as institutions continue to migrate the bulk of their originations to the online channel and the account opening process becomes increasingly faceless. While the solutions described above play a critical role in meeting compliance and risk management objectives, they unfortunately often fall short when it comes to detecting synthetic identities. Identity verification vendors were quick to point the finger at lapses in financial institutions’ internal and third-party behavioral and transactional monitoring solutions when the recent $200 million attack hit the headlines, but these same providers’ failure to deploy device intelligence alongside traditional controls likely led to the fraudulent accounts being opened in the first place. With synthetic identities, elements of legitimate creditworthy consumers are often paired with other invalid or fictitious applicant data so fraud investigators cannot rely on simply verifying data against a credit report or public data source. In many cases, the device used to submit an application may be the only common element used to link and identify other seemingly unrelated applications. Several financial institutions have already demonstrated success at leveraging device intelligence along with a powerful risk engine and integrated link analysis tools to pinpoint these complex attacks. In fact, one example alone spanned hundreds of applications and represented millions of dollars in fraud saves at a top bank. The recent synthetic ring comprising over 7,000 false identities and 25,000 fraudulent cards may be an extreme example of the potential scope of this problem; however, the attack vector will only continue to grow until device intelligence becomes an integrated component of all online account opening decisions across the industry. Even though most institutions are satisfying Red Flags guidance, organizations failing to institute advanced account opening controls such as complex device intelligence can expect to see more attacks and will likely struggle with higher monetary losses from accounts that never should have been booked.

Outsourcing can be risky business. The Ponemon Institute reports that 65% of companies who outsourced work to a vendor have had a data breach involving consumer data and 64% say it has happened more than once. Their study, Securing Outsourced Consumer Data, sponsored by Experian® Data Breach Resolution also found that the most common cause for breaches were negligence and lost or stolen devices. Despite the gravity of these errors, only 38 percent of businesses asked their vendor to fix the problems that led to the breach and surprisingly, 56% of the companies learned about the data breach accidentally instead of through security protocols and control procedures. These findings come from a survey of 748 people in a supervisory (or higher) job who work in vendor management at companies that share or transfer consumer data mainly for marketing, finance and outsourced IT operations including cloud services and payment processing. The survey also polled the vendors and 57% of them reported that they in turn, outsourced work to a third party. 23% of vendors could not tell how often data loss happened which is a sign that they don’t have proper procedures and policies in place to know when incidents occur. When asked about their data breach notification practices, only 16 percent of vendors said they immediately notified their client after the breach investigation with 25 percent saying they don’t even tell clients about breaches of data. Keeping all work and information in house is not feasible in today’s multi-corporate companies, and outsourcing is a business reality, however, all parties have a responsibility to protect the sensitive and confidential data that is entrusted to them. When outsourcing consumer data to vendors, here are a few guidelines companies need to follow to safeguard the information: 1. Make sure you hold vendors to the same security standards as your own in-house security policies and practices. 2. Make sure the vendor has appropriate security and controls procedures in place to monitor potential threats. 3. Audit the vendor’s security and privacy practices and make sure in your contract with them, the vendor is legally obligated to fix data problems should a breach occur including notifying consumers. 4. Monitor the security and privacy practices of vendors you work with especially if you share consumer data with them. 5. Require background checks for vendor employees who have access to confidential information. The goal of this study was to better understand what companies are doing to protect consumer data they outsource and where improvements could be made to insure privacy and security when sharing private information with third parties. The solution seems to be that all parties must first agree that data privacy and protection is paramount and then work toward the mutual goal of achieving responsible privacy and security practices. Download the Securing Outsourced Consumer Data report